September 25, 2018
Cyber-tales from the dark – and light – sides.
Hi folks!
Today I’ve got some fresh, surprising cybersecurity news items for you. The first few are worrying stories about threats stemming from a certain ubiquitous small device, which many folks simply can’t be without just for one minute – including in bed and in the bathroom. The last few are positive, encouraging stories – about women on the up in IT. Ok, let’s dive in with those worrying ones first…
Don’t join the Asacub victim club
These days, folks tend to entrust their (trusty?) smartphones with all sorts of stuff – banking, important work and personal documents, messaging (often with very personal details strictly for a few eyes only), and more. But, hey, you’ll know all this perfectly well already, and may be one of these folks to this or that extent yourself; and if you are – you really do need to read this one carefully…
At the end of August a sharp increase was detected in the proliferation of the Android Trojan Asacub, which exploits that peculiarly human weakness called curiosity. The Trojan sends a text message with words like: ‘Hey John: You should be ashamed of yourself! [link]’, or ‘John – you’ve been sent an MMS from Pete: [link]’. So John scratches his head, becomes as curious as a cat, wonders what’s in the photo, clicks on the link, and (willingly!) downloads an application… which then proceeds to stealthily access his full contact list and start sending out similar messages to all his peers.
But this crafty malware doesn’t stop there. It can also, for example, read incoming texts and send their contents to the hackers running the malware, or send messages with a given text to a given number. And the ability to intercept and send texts gives the authors of the Trojan the ability to, among other things, transfer to themselves funds from the bank card of the victim if the card is digitally connected to the phone number. And as if that weren’t bad enough – there’s a bonus for the victim: a huge bill from his mobile provider for sending all those messages to everybody.
So how can you protect yourself from such fearsome mobile malware? Here’s how:
- Don’t click on suspicious links;
- Carefully check which rights are being requested by the downloaded application (e.g., microphone, camera, location…);
- And last and most: the simplest step – install reliable protection on your Android smartphone.
Android? Hmmm. I can hear all the sighs of relief just now: ‘Aaaaahhhh, thank goodness I’ve got an iPhone!’!
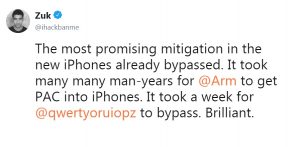
Hold your horses all you Apple lovers; here’s a couple of links for you too (don’t worry: you can click these – honest!):