May 25, 2012
The Dangers of Exploits and Zero-Days, and Their Prevention.
You don’t need to hear it from me that the Internet is a really interesting phenomenon, and mega-useful for all those who use it. But at the same time its openness and uncontrollability mean that a ton of unpleasantness can also await users – not only on dubious porno/warez sites, but also completely legitimate, goody-two-shoes, butter- wouldn’t-melt-in-mouth sites. And for several years already the Internet has been a firm fixture on the list of the main sources of cyber-infections: according to our figures, in 2012 33% of users have at least once been attacked via the web.
If you dig deeper into the structure of net-based unpleasantness, you always come across three principle categories of threats: Trojans, exploits, and malicious tools. According to data from our cloud-based KSN (video, details), the break-down is as follows:
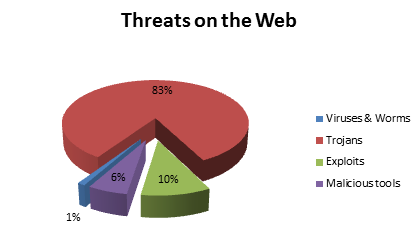
The ten-percenter in the above pie chart as you can see belongs to so-called exploits (their share will actually be greater in reality, since a lot of Trojans have a weakness for exploiting… exploits). Exploits are mostly exotic peculiarities to non-professionals – while a real headache for security specialists. Those of you more in the latter category than the former can go straight here. For the rest of you – a micro-lesson in exploits…
Software is designed by humans, and humans forget things and make mistakes. Plus, to date there hasn’t been invented a “perfect” method of programming. As a result, practically every bit of software contains vulnerabilities – that is, errors in its programming code via which attackers can take control of a system, mess it up, etc. And the code that exploits vulnerabilities in programs is called… wonder of wonders – an exploit.
So which programs are most often attacked by exploits? Here are our statistics for 2011:

(So much hassle caused by Adobe Reader. Eh? And all it does is display pdfs, as plenty of other programs do… Agh, the inhumanity.)
Vulnerabilities can be used by exploits, or go unexploited, depending on the popularity and functionality of the given program and, correspondingly, the level of attention it gets from the cyber-rascals. A typical example was the recent Flashback Mac-Trojan incident last month. The vulnerability was in Java, which was discovered as early as the beginning of the year, but the exploit for Mac appeared a month later. What’s important is that if a vulnerability in a specific program isn’t found – that doesn’t mean it doesn’t exist. It only means that (i) it’s used by too few folks for a vulnerability to be found by mistake, or (ii) it’s so insignificant a program that it’s not worth the bother (of the cyber-baddies) digging into it to search for mistakes.
A usual scenario goes like this: A vulnerability is discovered by a researcher, who reports it to the developer. The developer then urgently patches the vulnerability with… yep, a patch. Only then does the cyber underground pull itself together, come up with an exploit, and try to attack users who haven’t got round to installing the patch yet.
I write a usual scenario, but maybe it’d be better to describe such a scenario as what we’d prefer to have each time (with a time gap between the vulnerability’s discovery and the exploit’s appearance). I say this because what often actually happens is the exploit appears together with the first news about the vulnerability, or the developer (for example Apple in the Flashback incident) drags its feet in releasing a patch and as a result the exploit gets set into the wild before a patch becomes available. An exploit for which there’s no patch yet is called a zero-day exploit (zero days after (i.e., before!) the patch). And it’s zero-day (or 0-day) exploits/attacks that are the nastiest variety.
Here’s some interesting info on the geographical distribution of sources of web attacks, the majority of which use exploits:
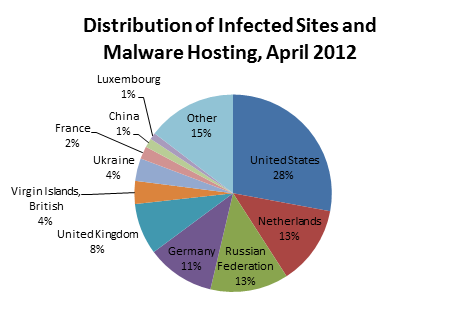
The location of an attacking site does not necessarily mean that who’s behind the attack is also from there. Far from it. The cyber swine can easily register a site to a front company or non-existent individual abroad and conduct the malicious activity from there.
Now, two of the most widespread methods of attacks via exploits are:
- Drive-by downloads (85% of all attacks via the Internet). These entice you to a site which, with the help of an exploit kit, scan the browser for vulnerabilities and, if found, unnoticeably infect the computer. This method is widely used in mass attacks for reaching the maximum destructive effect. Approximately in a third of cases, the attacking site turns out to be a legitimate website of some respected organization of other, which was hacked and injected with a special malicious code.
- Targeted attacks. Here, a user unsuspectingly (foolishly? :) launches an infected file (for example, a pdf), which scans the installed software it runs on (in the pdf example, Adobe Reader) for vulnerabilities, and, if found, infects the computer though them. The file itself can be delivered by all sorts of different routes – e-mail, web file archives, USB sticks, etc. Targeted attacks are precision attacks with a particular pinpointed target – like the missiles taking out those Range Rovers at the end of Syriana – not mass attacks of anything and everything (like carpet bombing). Targeted attacks are also sometimes called Advanced Persistent Threats (APT). They target specific individuals or organizations and distinguish themselves by using sophisticated social engineering techniques.
Now here’s the thing: the 10% share of Web-originating threats coming from exploits in our statistics (first pie-chart – above) in actual fact amounts to just as much of a problem as the 83% share of threats coming from Trojans! For example, at the moment the most widespread exploit kit is one called Blackhole, which is able to infect over 30% of the computers visiting a compromised website (depending on the traffic, installed software and security). Not a single Trojan could ever even dream of such a figure!
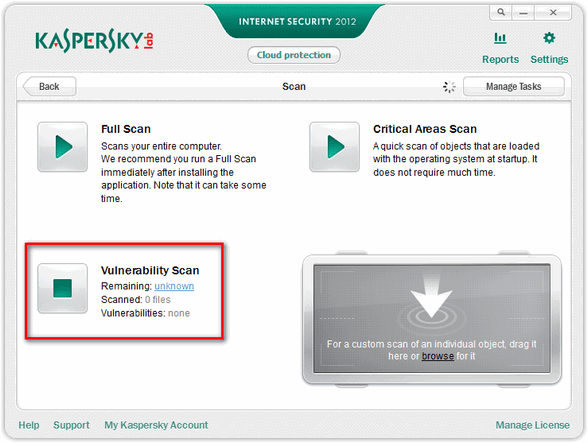
We’ve been fighting exploits for years now, with an impressive success rate. Our products have a dedicated database containing signatures of known exploits, malicious URLs via which infections are loaded, and also special heuristic and proactive technologies for detecting the future challenges of this type of threat. If this kind of malicious code is found, the program is blocked, the user and sysadmin are warned, and the actions of the attack are rolled back. We also provide a very useful feature for on-demand scanning for the presence of vulnerabilities:
And now for a spoiler about a very tasty morsel of a feature in the upcoming version of KIS/KAV. With the release of the new version of our Endpoint Security in the first quarter of next year it will be accessible to corporate users too. As you’ll have guessed, this feature has something to do with protection against exploits. To be more precise – against unknown exploits, that is, those same zero-days!
I often get asked how it’s possible to provide protection against something that’s unknown. My answer is always: by closely observing evolving threats. We have about a thousand top-notch R&D specialists all around the world who model threats, research trends, and generally in all sorts of weird and wonderful ways think about tomorrow’s world and your computer’s security in it.
First of all we have one of the most progressive multi-level arsenals for the fight against future threats – emulation, heuristics, HIPS, behavior blockers, cloud-based reputation services, whitelisting, application control, and a whole array of proactive technologies. Secondly, “unknown” in computer security speak is not as mysterious and inconceivable as in real life!
Of course there’s always some likelihood of the appearance of some absolutely new kind outbreak, which can hardly be foreseen or proactively protected from. But in the majority of cases maliciousness generally acts according to a certain pattern of conduct and uses particular tools. And this is how we catch them out! And as experience shows – rather successfully.
So, what’s that tasty morsel for protection against unknown exploits in KIS/KAV 2013 going to be?
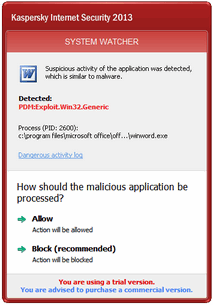
Here’s what: we’ll significantly improve the System Watcher module (which monitors programs’ activity) with new Automatic Exploit Prevention (AEP) technology. Its title is fairly self-explanatory as regards what it does, but preceisly how it does it requires some detail.
Actually, AEP is the umbrella name for a whole spectrum of anti-exploit features. First, we added to our database special patterns of exploits’ behavior. System Watcher uses these templates for controlling the actions of applications (for example, browsers) and detecting suspicious activity and blocking it. Second, the system tracks the source of the files and counteracts the drive-by downloads. In addition to that, we’re integrating the Attachment Execution Service (AES) and distinguishing files created with and without the knowledge of the user. Third, for the most critical programs and extra modules (for example, plugins for browsers), we’ll enforce using ASLR technology. Each time it’s used, ASLR changes the structure of the address space of attacked programs in a random way. As a result, even if an exploit exploits a vulnerability, it won’t be able to launch the malicious code, since it won’t know its exact location!
AEP is currently being tested and showing impressive results. We put through it a whole mass of exploits for Flash Player, QuickTime, Adobe Reader, Java and other programs – and we got a 100% detection rate! Especially fab was the successful detection of an exploit for the recent well-publicized vulnerability in Windows Media Player: the exploit allowed to infect a computer via a specially created MIDI music file, and worked on all versions of Windows from XP onwards. What’s critical here is that thanks to AEP we catch 100% of the exploits of the Blackhole exploit kit while the industry’s average score is only 94%.
To conclude, a few more preventive measures – in addition to the above-described technologies.
As they say, put your faith in the antivirus, but don’t mess up yourself. By this is meant key in prevention is abiding by simple rules, like “wash your hands before eating”. An attack of malware or an exploit in the above-described way is possible via all sorts of suspicious sites. Think long and hard before visiting these porno/warez sites – are they really worth the risk? And of course, never forget the golden rule of computer hygiene: don’t under any circumstances open suspicious attachments.