August 30, 2011
Great GReAT Guys: Aleks Gostev in the Spotlight.
I’m glad the first part of our In-the-Spotlight series featuring Costin G. Raiu received so much attention and positive feedback on both Twitter and Facebook.
My special guest today is Aleks Gostev, Chief Security Expert at KL and highly valued member of the company’s Global Research & Analysis Team (GReAT).
Aleks is a unique multi-disciplinary infosec guy – one of the world’s most prominent security experts, who regularly appears in the mass media in interviews or writing op-eds. He became involved in anti-malware research in 1996 when he founded an anti-virus expertise center in the Komi Republic – a large territory in the North-West of Russia. Since 1998 he’s been Project Coordinator of Wildlist Russia – an initiative aimed at collecting and analyzing data about malware outbreaks in the country.
We first met in 2002, and I recall I felt he was the right guy for the company from the word go. Our first chat went something like:
– Married?
– Yes.
– Birth date?
– Mine or the wife’s?
Nice! That convinced me to give him a job tout de suite, and frankly speaking I’ve never regretted it. Aleks’ first big assignment was dealing with the notorious Slammer (Helkern) worm, which caused a major Internet outage in South Korea and infected hundreds of thousands of computers worldwide. He managed the case perfectly: we were one of the first AV companies to report the outbreak and provide protection.
Aleks founded and led the Global Research & Analysis Team (GReAT) from 2008 before moving to his current position as Chief Security Expert with the team in 2010. Aleks analyzes all aspects of information security, with a focus on new threats and global outbreaks. His responsibilities include deep investigation of new malware and expert positioning of Kaspersky Lab. He is also editor-in-chief of Securelist. Before joining the company in 2002 he held various IT and security related positions in both public and private organizations.
You can follow Aleks on Twitter (@codelancer) and read his personal blog at Securelist.
He also does lots of rock climbing, traveling and extreme sports:
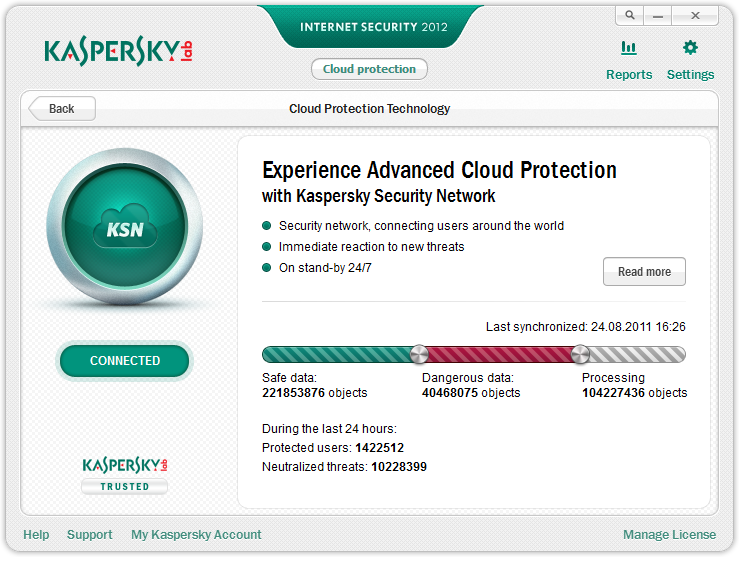
However, in this spotlight piece we will concentrate on Aleks’ expertise in cloud security.