January 28 is my aunt Olga’s birthday. It also happens to be Data Privacy Day. And my aunt Olga still isn’t aware! But she should be! For digital data is the currency of the new millennium. Accumulated knowledge of trillions of clicks and transactions – it’s a gold mine for any business. And multimillion-dollar businesses – lots of them – are based on the sale of these cyber-resources.
Global IT companies have more access to personal data than do countries. As a result, this topic is extremely important; it’s also toxic.
And, wherever there’s money – there are always bad guys. Cyber-bad-guys getting up to no good with folks’ data are forever multiplying in numbers. But even respectable companies may get up to no good with folks’ data too, and they seem to get away with – mostly. But more on that later…
Now, I’d like to ask a simple question – one to which, at least in global IT, there is no answer yet: ‘What is good and what is bad?’ I mean: where is the line between universal human morals and business ethics? Where is that fine line?
Alas, the question of cyber-ethics and cyber-morals is a very ambiguous one. Meanwhile, I can assure you that with the introduction of 5G and further sharp increases in the number of IoT devices, our data will be collected all the more. And more, and more…
Now for some detail: broken down into the main, most-pressing, interesting matters:
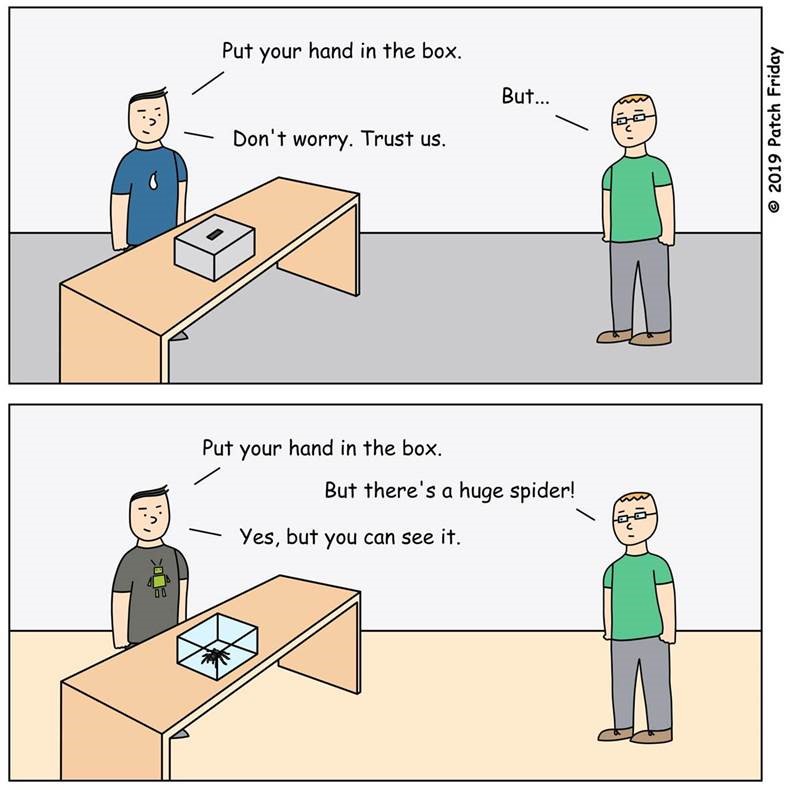
Lawyers, lawmakers, journalists, politicians, pundits, social commentators, philosophers… – not one of them can answer this question: ‘Who does data belong to?’ To users? To governments? To businesses? It would nice to think that users’ personal data belongs to those users themselves; at least up until when they may decide to voluntarily share it: when they fill in a form on a website, enter their name, telephone number and email to register for a newsletter, or thoughtlessly place a check in an app without reading through the small print of a lengthy legal agreement. Formally, from that moment on we give certain third parties the legal ability to handle our data, analyze it, sell it and whatever else is written (but rarely read) in the respective agreement. So does that mean that from that moment the data belongs to those third parties, too?
Much of the problem lies in the fact that the term ‘personal data’ is very vague and ephemeral – not only from the standpoint of the user but also from the legal one. Laws often can’t keep up with technological development. Nevertheless, on the whole over recent years the tendency has been clear: new laws being passed on the protection of personal data and the updating of existing legislation. In parallel, people’s attitudes toward personal data and privacy have become a lot more serious – something that of course I’m very happy to see.
Enough of my ‘intro’; let’s move on to the main dish…
Last week there was quite the scandal reported in the press involving Avast, one of the major players in the AV market.
Vice published an expose detailing how Avast has for years been giving data of its users that it collects to one of its subsidiaries – Jumpshot – which in turn then sells it to third-party companies. Those third-party companies thus got access to information on the online behavior of users: what websites were visited, movements from sites to sites, GPS coordinates of users of Google Maps, YouTube viewing histories, and lots more besides. And though the data wasn’t associated with specific individuals, IP addresses or emails – in other words it was anonymous – the data did come with identifiers, which keep working up until when a user may delete their Avast antivirus from their computer
Of course, this is nothing short of scandalous from an ethical point of view. We here at K have never allowed such a thing to happen, and never would; and we firmly believe that any earnings made from data of your users is simply beyond the pale.
The epilogue of this sorry tale was a formal apology from Avast’s CEO, in an announcement about the termination of Jumpshop. In my view, that was the only appropriate thing to do. I understand it mustn’t have been easy, and there will have been big financial losses, but still. Well done for doing the right thing in the end.
For us, the matter of data storage and its usage has long been a priority. Back in 2017 we launched our Global Transparency Initiative, moved our data processing for European users (plus other countries) to Zurich, since then have opened two more Transparency Centers, and are soon to open two more. Projects like this aren’t cheap; but we feel we simply must set new standards of openness and a serious attitude to personal data.
More details about our principles of data processing, about how our cloud-based KSN works, anonymization of data, and other important things you can find here. But I just want to add, addressing all our users, that, rest assured: we never make any compromises with our conscience – ever.
Often, the collection and sale of data is carried out by free antivirus software, covering things like surveillance of users for advertising purposes and the trade in their confidentiality, all to make money. As you’ll know, we also have a free version of our AV, based on the same protection-tech as our other, paid-for products, whose effectiveness is constantly confirmed in independent tests. And though the functionality of the free version is rather stripped down, it’s still a piece of AV we’re very proud of, delivering users solid and reliable protection and leaking no personal data for advertisers. Users deserve the best protection – without annoying adverts and privacy trading. But I’ve been saying that years.
Something else I’ve been talking about for years is my own paranoid very serious attitude to my own personal data. One more time: I only ever give it out when it is wholly necessary, which I recommend you do too. I understand it’s difficult to fully realize the importance of this, when its so intangible and when the ‘price’ of our data is impossible to estimate. Just remember – every click, every site you visit – someone (rather – something), somewhere is making a record of it, and it never gets deleted. So come on folks, lets get serious about our digital footprint; and more serious about how we view the companies and products to which you entrust your personal – private – data.
PS: We recently launched a useful site with detailed recommendations for protecting your personal digital life. Here you can find the most important privacy settings for popular social networks, online services and operating systems. Have a look!