April 11, 2025
AI-Apocalypse Now? Nope, but maybe later…
What exactly is artificial intelligence?
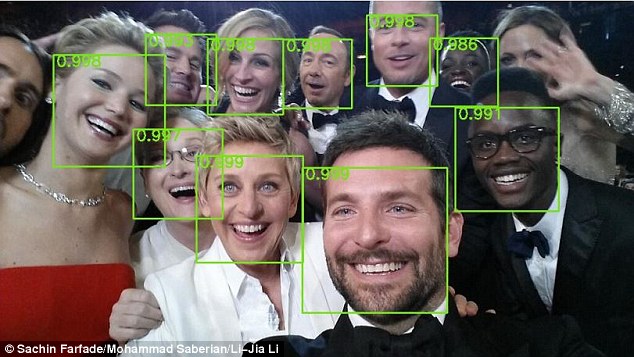
These days the term is slapped on practically anything software-driven that runs automatically. If it can do something by itself, people break into a cold sweat and are ready to swear eternal allegiance to it. In reality, the term “artificial intelligence” has different interpretations depending on the level of self-awareness across various layers of the population of our planet. For example, there are the rather primitive definitions in online encyclopedias, where AI, I quote, “refers to the capability of computational systems to perform tasks typically associated with human intelligence, such as learning, reasoning, problem-solving, perception, and decision-making”. This means, for example, that being able to play checkers or chess falls under the AI definition – even if the program can’t do anything else: no bike riding, no potato peeling, no pizza delivery routing…
However, the collective [un]consciousness believes that these IT novelties with “smart” features are indeed the very “digital brain” seen in Hollywood movies – capable of anything and everything, now and forever. It also believes that, soon, we mammals will have to go and hide in caves again – just like in the dinosaur era. Likely? I, for one, don’t think so…

The modern popular belief in an all-powerful AI – it’s all pure nonsense: about as ridiculous as ancient tribes’ terror during thunderstorms – thinking the gods were battling over their divine goals and motivations.
Neural networks, machine learning, ontology, generative AI, and other programming stuff – that’s the current level of “digital intelligence”; nothing more. These are programs or software-hardware systems designed to solve specific tasks – trained, steered, and fine-tuned by human experts. They’re not even trying to be universal – current tech just can’t handle that!