May 23, 2016
Darwinism in IT Security: Adapt or Die.
“It is not the strongest of the species that survives but the most adaptable to change.”
– Charles Darwin
It’s been a while since I’ve opined on these here cyber-pages on my favorite topic – the future of IT Security, so here’s making up for that. Get ready for a lot of words – hopefully none too extraneous – on the latest Infosec tech, market and tendencies, with a side dish of assorted facts and reflections. Popcorn at the ready – off we go…
I’ll be writing here about ideal IT Security and how the security industry is evolving towards it (and what’s happening along that evolutionary road towards it), and how all that can be explained with the help of Mr. Darwin’s theory of evolution. How natural selection leads certain species to dominate, while others fall by the wayside – left for the paleontologists in years to come. Oh, and what is symbiosis, and what are parasites.
I’ll start with some definitions…
Almost-Perfection in an Imperfect World.
Perfect protection – 100% security – is impossible. The IT Security industry can and should of course aim for perfection, in the process creating the best-protected systems possible, but each inching nearer 100% costs exponentially more – so much more that the cost of protection winds up being greater than the cost of potential damage from the harshest of scenarios of a successful attack.
Accordingly, it’s logical to give the following definition of realistic (attainable) ideal protection (from the viewpoint of potential victims): Ideal protection is that where the cost to hack our system is greater than the cost of the potential damage that could be caused. Or, looking at it from the other side of the barricades: Ideal protection is that where the cost of a successful attack is greater than the gain attackers would receive.
Of course, there’ll be times when how much an attack may cost doesn’t matter to the attackers; for example, to state-backed cyberwar-mongers. But that doesn’t mean we just give up.
So how do we develop a security system that provides realistic (attainable) ideal (maximum) protection?
Modern defenders vs traditional: think about adversaries not incidents, by @johnlatwc #TheSAS2016 pic.twitter.com/gss5MITuO1
— Eugene Kaspersky (@e_kaspersky) February 8, 2016
The Survival of IT’s Fittest – the Theory.
One of the key principles of Darwinism is genetic variation. Because of a recombination of genes, mutations and other unknown reasons, live organisms acquire new traits. And as time passes, the lucky ones in terms of new traits (the fittest ones) proliferate, while the less lucky get marginalized and eventually disappear. It’s why bears in the Arctic are white and in Kamchatka are brown.
A similar thing happens in IT Security: the cyber-rascals are constantly finding new vulnerabilities in computer systems and inventing new attack methods to steal data or money from the folks or companies that own/use those computer systems.
Whichever is the smartest and fastest group of cyber-rascals – the fittest – gets an underground following and thrives at the top of the cyber-underground kingdom by getting paid the most for their ‘patented’ criminal know-how. That group evolves into something bigger and stronger, while the others die away. The only difference to Darwin’s biological evolution is the speed of change – not millennia here but just several months for as many generations of threats to evolve.
To create a superior security system that provides ideal (maximum) protection, right from the outset developers need to envision the most devilish of all the most fiendish scenarios possible – scenarios so hellish that it’s quite unlikely they’d actually come about (it’s hoped, at least). Building protection with such apocalyptic attack scenarios in mind ensures two key things: it stops both dangerous optimism and hoping for the best. Also, keeping the very worst-case scenarios in mind from the outset helps not only in recognizing the problem, but also in understanding its scale and to develop the optimal strategy for dealing with it. If you know your weakness, you’re no longer the hunted; you’re the hunter.
Ok, that’s all very nice and logical in theory, but can it all be put into practice? How can you be a step ahead of these rascals and second-guess their next step?
Adapt – or Die.
The wise move to make in an environment of prevailing entropy is to come up with an adaptive model of conduct. One starts conducting oneself proceeding from analysis of the prevailing situation/environment on the basis of a limited amount of confirmed data (often in its absence) and a multitude of hypotheses. Each iteration of the ‘analysis – action – result’ cycle reduces ambiguity, and increases the rationality of conduct, performance and other parameters that are significant for business.
We started employing such an adaptive model in IT Security in 2013. The following year we found that this approach had been matched by Gartner’s vision of ‘adaptive security architecture’. This architecture is based on the cyclical application of tools from four basic cyberattack-related domains: preventive, detective, retrospective and predictive. Adopting such a model allows to create optimal protection that corresponds to the life cycle of cyberattacks – a model that’s able to quickly adjust itself to changing internal and external conditions.
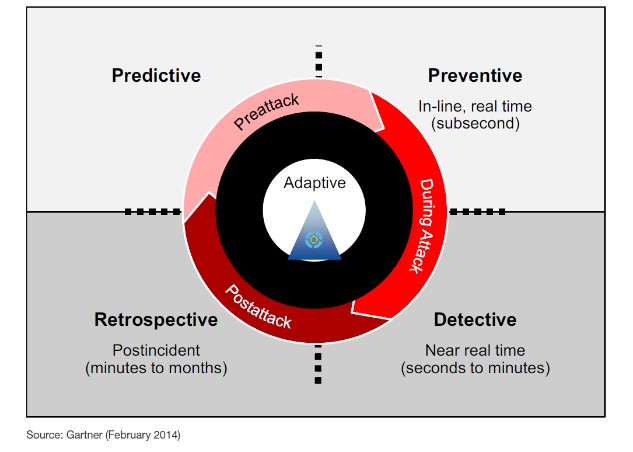 Source: Designing an Adaptive Security Architecture for Protection from Advanced Attacks, Gartner (February 2014)
Source: Designing an Adaptive Security Architecture for Protection from Advanced Attacks, Gartner (February 2014)
Since 2013 adaptive security architecture has been the cornerstone of our product strategy. Though early on we suffered quite a few teething troubles, we persevered; we knew it was the right approach for better protecting enterprise customers’ networks and solving their pertinent security issues. Though not much time has passed, already we’ve made great strides towards implementing our plans.
Houston, We Have a Problem.
So how are things looking now with actually getting adaptive security architecture applied in the enterprise world?
To be perfectly honest, not great.
On the one hand, there are very few vendors able to come up with all the elements to enable the creation of an uninterrupted cycle of adaptive security. Different pieces of the puzzle turn out to be not all that compatible with each other and are all the more difficult to combine into a single, central system of control.
On the other hand, customers are focused on particular domains of the cycle (mostly on prevention), and tend not to appreciate the importance of the others and of the complex as a whole. Such an erroneous outlook of customers is made worse by certain security vendors, which announce the creation of magic panaceas against all cyber-bad.
In the end we get an illusion of security, bewilderment after the latest incident, and a vicious circle of emergency-incident-sorting and constant-threats-to-business leading to increased spending on IT security (with no increase in its effectiveness) and a degrading of the value of IT systems.
In Darwinism, change is one of the propelling forces for biological development. Change is also a propelling force in IT Security – propelling it forward to stay ahead of the bad guys, and if a paradigm shift is necessary, so be it. That shift is under way: both the IT Security industry and customers are recognizing the problem (the necessary ‘first step’) and are on the right path. At KL, our particular approach to this necessary pivotal change is as follows.
Time for Fuel Injection AND Turbo Charging – but No Go-Faster Stripes.
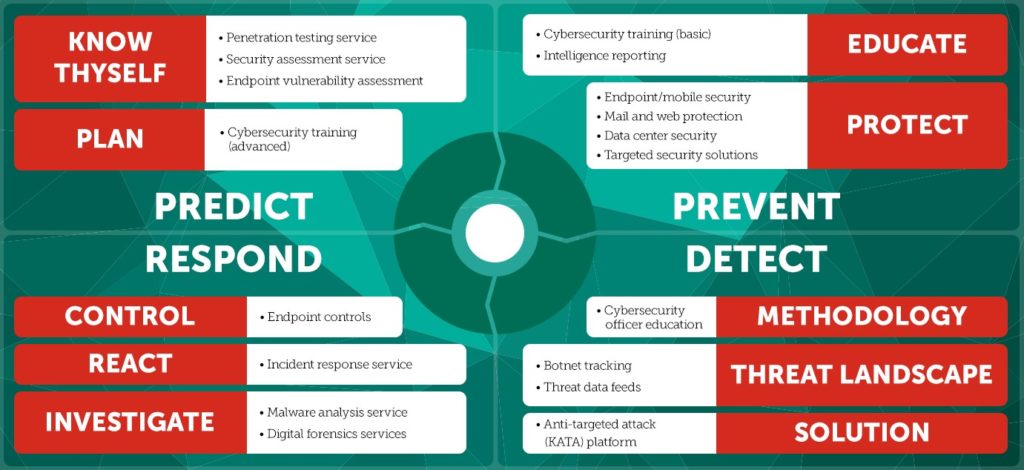
First of all we launched a wide range of services to strengthen our positions in all domains of the model. Now our portfolio contains the following: training of personnel of any level, threat intelligence, penetration testing, incident analysis and recommendations for clearing up after them, and a lot of other things to give us the complete cycle of ‘prevention, detection, reaction and prediction’.
From the product point of view, we complemented our traditional strong position in the domain of ‘prevention’ with a solution in the domain of ‘detection’ for protection against targeted attacks (Kaspersky Anti Targeted Attack Platform), and its integration with SIEM systems. And in the nearest future there’ll be the launch of a fully functional EDR (Endpoint Detection and Response) solution, which will gather into one ‘big picture’ different events across all machines of a network.
So, very soon we’ll be delivering a full spectrum of products and services for the creation and ongoing support of adaptive security architecture. Its main feature is the super-sensitive threat analysis systems: with sensors all around the network and on all nodes we’re able to present to the customer several-fold more data for taking informed decisions. Add to that both our human and machine-based expertise, and the effectiveness of the fight against complex targeted attacks will be significantly greater.
The main thing: customers don’t need to – and shouldn’t – dive in at the deep end when considering introducing such a system. It should be approached in stages, steadily – evolutionarily, according to Darwin’s theory as and how the peculiarities of the particular business, IT infrastructure and other specific details demand. Experience shows that customers prefer to kick things off with services (training and field reports), and add new pieces of the overall adaptive security puzzle gradually as they go along.
To Be Continued…
I’ll make no secret of the fact that we aren’t the only ones consistently developing new generation adaptive IT security. However, I’m very pleased we’re right up front, which is most encouraging and motivating.
Customers don’t care what a product is called or how pretty it looks on YouTube or in marketing materials. The only thing that matters to them is that, all other things being equal, they get the greatest chance of avoiding incidents and the accompanying losses. And that means we’ll just keep on toiling away at adaptive security – to give the market more than it expects.
That’s all for today folks. Coming shortly in a follow-up piece, I’ll be writing more on natural selection and the fight for survival – plus the inevitable… mutations.
.@e_kaspersky talks about the adaptive security model and the future of IT SecurityTweet