December 7, 2016
A Billion in the Cloud.
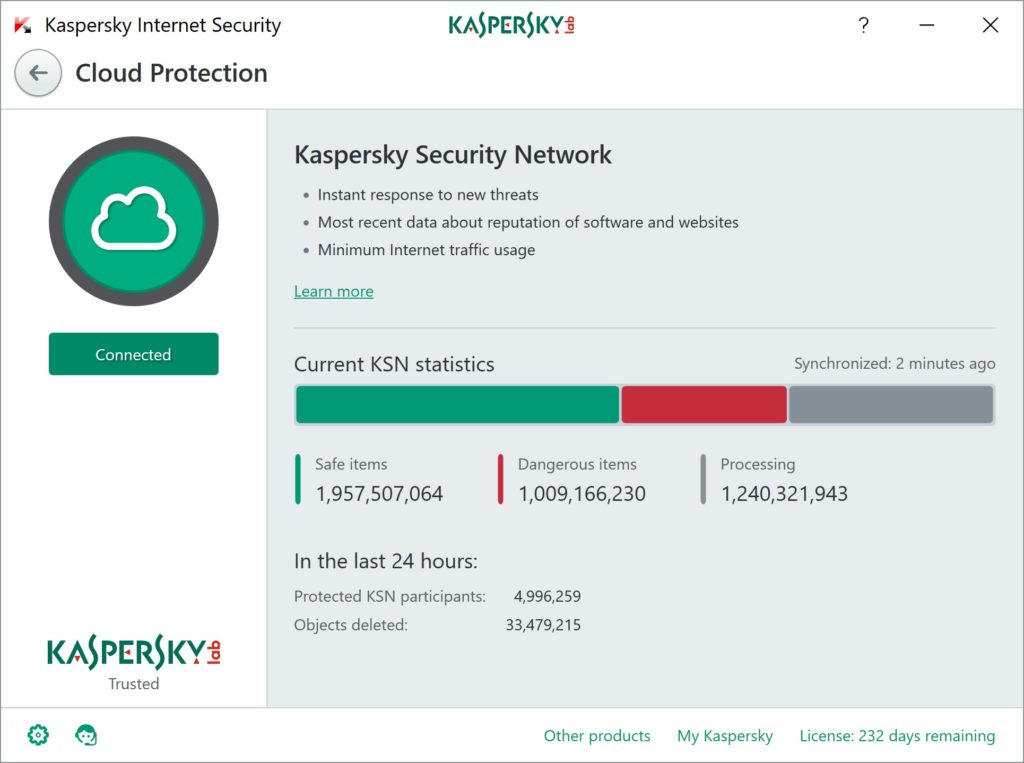
Recently, sharp-eyed users congratulated me with a ‘billion’ items in the Kaspersky Security Network. Thank you! Although, I need to explain what that ‘billion’ is.
First of all, don’t worry. This is not a billion something or other you don’t want on your computer; no, it’s something different, and it’s a little complicated. So let me start with some basic definitions.
An ‘ideal cybersecurity product’ is one that:
– Detects 100% of cyberattacks (and makes no mistakes);
– Consumes 0% of system resources;
– Does not bother the user with technical questions.
Of course, this sort of protection has not been invented yet. Therefore, the quality of a product is determined by how close it gets to the ideal.
To do this, we use a number of approaches, and Kaspersky Security Network (KSN) cloud technology plays a major role here. Because it’s ‘somewhere out there on the Internet’ KSN does not consume your computer’s resources. In other words, virtually any amount of data can be stored there, and it won’t hinder anyone. On the contrary: the more data is there, the better informed and, ergo, the more accurate are the decisions made by the automatic analysis systems powered by machine learning techniques. Bottom line: ‘billion’ stands for the volume of the cloud. That’s one.
Two. To ensure a 100% detection rate (or, more correctly, a detection rate as near as possible to 100%, the most diverse data about digital malefaction and technologies are stored in the cloud. Apart from file hashes, it contains malicious behavior signatures, statistical information, mathematical models of machine learning and many other things (but not everything, far from it). Thus, thanks to multi-tiered protection, a combination of tried-and-tested and new advanced technologies, we can automatically detect new cyberattacks. And we do so better than others.
Three. You may ask: how come there are a billion items in the cloud if there are only around five million records in the anti-malware databases on a protected computer? The point is that databases include all sorts of ‘generics’ (hashes, decision trees, heuristic procedures, behavior-based detection tools) to protect against cyber-junk in case the cloud is unavailable. One record can provide detection for an entire malware family (including similar malware that may emerge in the future) consisting of tens of thousands of specimens. But the KSN cloud remembers and keeps records of all detected objects, which is why there are many more elements in the cloud database.
That’s how it all adds up to a billion in the cloud. That’s a pretty impressive number alright. It demonstrates very well how fast things change in cybersecurity. Five years ago, there were ‘only’ 50 million items in this database. Back then, that was an awesome number; today, it’s almost laughable:
Nowadays, those 50 million items would be added to the database within a month or so.
It would be interesting to apply this number to the pre-computer age. Imagine a bookkeeper given the job of checking if there is a certain record in a ledger containing a billion records.
Let’s assume he can check 30 items a minute. How many hundreds of years would it take him? How thick is that ledger? How many calories would the muscles in his eyes consume, how many meals would he have to eat to provide the energy for this most interesting and useful work?
But before that job, the bookkeeper would have to look through an even larger ledger containing nearly two billion records about trusted objects!
Naturally, in the computer age, this sort of work is done almost instantly and without any human involvement. Also, the analysis process is optimized in every possible way: to provide the user with fast and reliable protection, we’ve invented expert systems to ensure maximum detection rates and minimum false positives. When handling a perfect storm of malware, machine learning is also essential – systems must teach themselves to better detect computer attacks. Of course, it also requires input from the engineers who build these algorithms, and then adjust and fine tune them.
Someone might ask: what’s the point of getting all excited about a billion items in a database? Isn’t it a bad thing that the number of cyberattacks is growing this fast?
Of course it’s bad, and that can’t be helped. I’ve said on many occasions that KL’s business is similar to looking after a cesspool – our job is to clean up the xxxx sewage systems of the Internet. Yep, it’s a dirty job, and most unpleasant at times, but somebody has to do it.
There was an advertising campaign by a certain laundry detergent featuring jolly kids covered head to toe in dirt – the slogan was ‘dirt is good’. The same applies to cybersecurity: dirt is good, but only when it’s been analyzed, described, and covered by protection technologies so it no longer poses a threat to anyone.