October 4, 2016
Features You’d Normally Never Hear About – 2017 Reboot.
We’ve been ‘saving the world’ for, hmmm, now let me see, a good 19 years already! Actually it’s several years longer than that, but 19 years ago was when we registered KL as a (UK) company.
Alas, ‘saving the world’ once and for all and forever just ain’t possible: cyberthreats are evolving all the time, with the cyber-miscreants behind them forever finding new attack vendors across the digital landscape, meaning that landscape will never be 100% safe. However, hundreds of millions of folks all around the world, on different devices and in different life situations, each day have the possibility to protect their privacy and data, safely use online stores and banking, and protect their kids from digital filth, cyber-perverts and con-artists.
And on our side – the ones doing the protecting – there’s plenty of raison d’être for our experts: each photo rescued from ransomware, every blocked phishing site, each shut down botnet, and every cyber-bandit sentenced to prison: each one = cause for professional satisfaction and pride. It means all the hard work wasn’t for nothing; we really are doing good.
In the struggle against cyber-filth, cyber-perverts and cyber-crooks, we’ve got for you a range continually improved tools.
In the new versions of our home products – the 2017 incarnations – there are a lot of new useful features. Some of the features are very ‘out there’ – extrovert, if you like – so you’ll hardly miss them. However, some other features are distinctly introvert by nature, sometimes to the extent of being almost invisible; not that their shyness makes them any less useful – they are part and parcel of the very wholesome whole – a whole now known to equal the best protection in the world, no less.
As you might have guessed already, here in this post I’ll be telling you a bit about these quieter, modest types that reside under the hood of KAV/KIS/KTS-2017 – incidentally reanimating the series ‘Features You’d Normally Never Hear About‘, which hasn’t seen the light of day blog since early 2012.
First off, let’s remind ourselves what modern protection from cyberthreats is.
Modern protection from cyberthreats is a complex, multi-component mechanism. It’s like the multi-armed Shiva (only with a lot more arms than her eight or so:), bringing together hundreds (!) of different technologies. Or, it’s like a Swiss Army Knife – the fattest one with everything on there, including the kitchen sink – to be able to cope with any possible scenario, and even as yet impossible ones. And each knife (and spoon and other included device) plays a role in the overall protection provided. Moreover, those knives are sharper than… a Valerian steel sword!
Traditional signatures – that is, ‘portraits’ of specific malicious programs – have been pretty obsolete for years already in the cybersecurity industry. Maliciousness has grown to such an extent that, if signatures were still key in antivirus, an antivirus database worth its salt would ‘weigh’ more than… a complete collection of all the movies Hollywood’s ever made!
In our case, the antivirus database in the product is a collection of complex technologies, each of which is intended for catching hundreds of thousands of malicious programs and dangerous websites. These are robots that are able to automatically and without the input of an expert recognize and neutralize unknown cyberthreats.
For example, the robot called PeForest, born and raised in the best traditions of machine learning, meticulously studies all unknown objects it comes across, and decides for itself whether they’re malicious or not.
So how does it manage it?
Easy (well, ok… not very): while still learning in the lab the robot undergoes training using millions of both clean and malicious files so that it learns how to recognize them based on a multitude of hallmarks. Later, after graduating from ‘school’ and out on the cyber-battlefield, PeForest – sat in the AV on your computer – relies on so-called decision trees in its analysis to eventually make a decision as to whether to exterminate the file or let it remain free.
In the new 2017 versions there are many such robots; actually, not quite ‘in’ the products: most of the robots actually reside in the cloud (KSN) so as to not put too much of a load on the user’s computer.
We’ve been using machine learning to bring up these robots since the mid-2000s. That could sound like it’s obsolete then, in the fast-moving world of cutting-edge tech. Nothing could be further from the truth: the longer you work at machine learning – the better, plain and simple. Not using machine learning in cybersecurity today would be just unthinkable, impossible, crazy. It’s so crucial today that it’s the one area into which most resources are pumped.
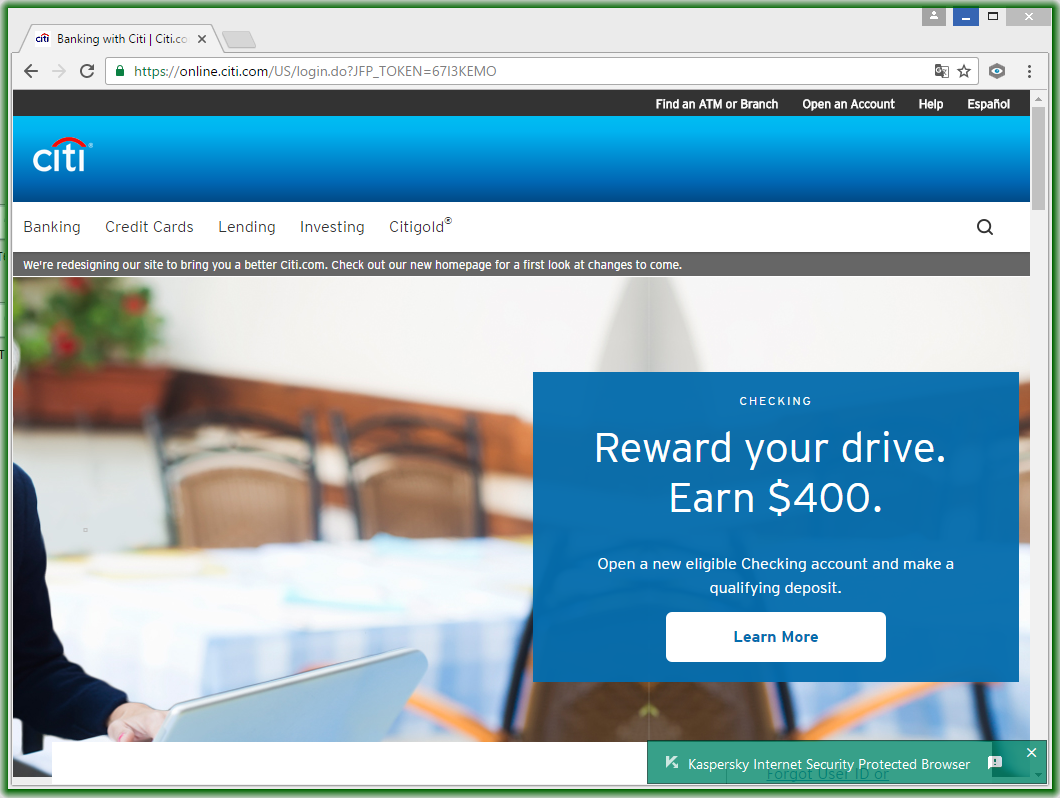
For example, using neural networks, robots automatically and with a high degree of accuracy recognize phishing websites, even if they’re exact doppelgangers of the genuine sites.
And one of our new robots, called CEREBRO, surfs the Internet all day and night scanning for malicious code, and when it finds some, it automatically categorizes it based on its content and sends the info on it to KSN, where other robots – also automatically – can apply protection for you. CEREBRO, a robot-crawler, has already scanned around a hundred million webpages (and doesn’t forget to keep rechecking them, just in case something’s changed).
There’s also the robot whose sole job is going walkabout around Google Play and scanning apps there. It already knows all about ~90% of the online store, and is continuing to hunt/scan as we speak. And this is what I mean: we’ve countless other such features robots you’d probably never hear about.
But here I need to make a proviso: no matter how important and increasingly popular machine learning is in cybersecurity, the most important role in the development of protection is that played by human beings – experts, to be more precise.
Who else would direct robots’ ‘brains’, teach them what to do, and how to catch the cyber-nastiness? Cyber-reprobates learn quick, so even the quickest and most highly-trained robot after a few months will start doing a sloppy job. Therefore the experts have to regularly give ‘refresher courses’ to the robots, if not full-on post-graduate ones. In short: human brains are still vital.
One more new feature that’s mostly invisible to the eye is File Categorizer. It automatically determines the category of a program (browser, game, media player…) or site being opened and acts according to the set security policy. For example, Parental Control kicks in to block an application unsuitable for kids, or turns on Safe Money to secure online banking. And like the other technologies mentioned here, it’s small, quiet, and introverted – but oh-so important.
The fight against cyber-evil is an ongoing fight. Experts are continually thinking up new smart technologies, to make cyber-thugs’ life more difficult. The features I’ve mentioned above are only the tip of the iceberg of the ‘under-the-hood’ domain of KAV/KIS/KTS-2017. Moreover, with every new year that tip of the iceberg is completely changing, with more and more processes migrating over to machine learning. What remains the same is our striving to stay one step ahead of the cyber-villains – so that you can say: