September 15, 2011
Features You’d Normally Never Hear About.
For different reasons, announcements of new products often never go into the finer details of those products, and leave out info on the slightly less significant though still immensely useful features that go towards making a product complete. However, thanks to our press releases and press conferences, we get the chance to delve into the tasty, lesser-known, more introverted features that might normally pass you by.
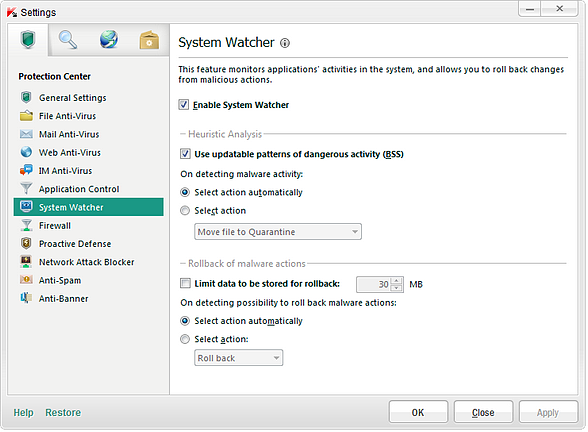
First up out of these small but irreplaceable vita-features is System Watcher, whose main function is monitoring applications’ activity on a computer.
If you are told that the anti-virus industry is plateauing out, has come up with nothing new of late, and is generally not able to hold its own in the fight against cyber crime – don’t believe it. As far as I see, all we ever do is search for (and find and then apply) new technologies other than traditional anti-virus signatures. And System Watcher is a perfect example of this.
The feature isn’t new. The first version was introduced in our home products in 2009, and back then it had just basic functionality. By 2010 System Watcher had already grown up and gotten better and wiser. In the latest product range, it has been strengthened and improved yet further. Yet what is still curious is that the majority of competing products of other companies still don’t have anything similar, while just a few others have introduced it only in their latest releases!
Anyway, let me tell you all about this feature in some detail.
What exactly is System Watcher?
Well, it’s a component inside our home products (specifically, KAV, KIS and PURE). It will soon be featured in all our corporate products too. The component analyses the activity of all installed software on a computer in real time. Should changes be made to the system register, boot sector, or a file (beside hundreds of other alterations), they all get logged in System Watcher’s database. As a result, it’s easy to restore a system to its original, uninfected state – a process called rolling back. The creation, deletion, or alteration of files, plus changes to the register, boot sector, config files, and much more besides can all be rolled back.
But System Watcher is not just a brainless logger of events.
First, it has a set of BSS (Behavior Stream Signature) patterns – behavior profiles of malicious activity used to identify unknown malware.
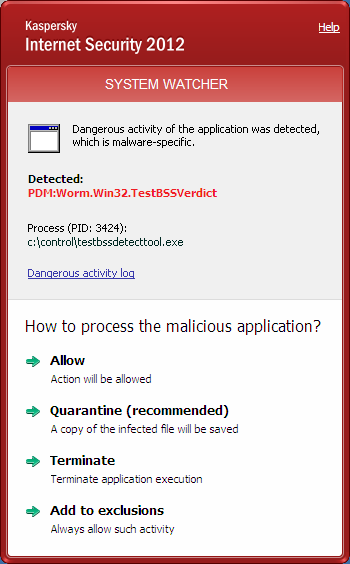
Second, it exchanges information with other components of the product and remembers chains of events to form a comprehensive picture of activity – keeping track of every program and program groups. And this has markedly increased the accuracy of detection and overall protection. Thus, all it needs to do is discover a single malicious action to be able to understand the whole picture of the penetration, to elicit the malicious components, and restore the system.
For example, let’s say a previously unknown Trojan has infected a computer. Shortly later, a module of the Trojan gives itself away by installing a suspicious connection. System Watcher instantly detects this, observes what the module interacted with, reveals all the other modules of the Trojan, and finds the responsible party. Then it rolls back the changes and together with the file anti-virus (another component of our products) deletes the Trojan. It all resembles a high-level diagnosis of House M.D. on the telly. Like him, System Watcher examines, locates and names the problem, and then sends the patient off to the surgeon.
So what’s new in System Watcher of the 2012 vintage?
First of all, the number and different types of monitorable events in the database have been increased.
System Watcher analyses not only activity of programs, but now the work of system services too. Even the printing service comes under the microscope, since there exists malware that uses this service to get inside a computer. Other new events covered include controlling MBR modifications, operations with the Windows subsystem, symbolic links, internal command transfers, interception of OS reboots, and a ton of other stuff.
“Why go to all that trouble?”, you might ask. Well, what about, for example, the malware that can delete or copy a file by getting someone else to do the dirty work – simply by adroit manipulation with Notepad? But that’s just one trivial example. Basically, the essence of System Watcher is that, as we say in Russia, “you can’t spoil the porridge with too much butter”, in other words – you can never have too much of a good thing: the more events we cover, the fuller the picture we have, and the better we are able to pinpoint infections. And all the while system performance is practically unaffected.
Importantly, System Watcher now tracks actions of programs throughout their full life cycle, that is, not only during current but also previous work sessions. The signature database is configured to accommodate 100 MB of data, which is more than enough for a month’s history, though the size can be customized.
And last but not least: System Watcher is integrated with our cloud-based security network – KSN (video, details) – with which it exchanges data on suspicious actions (of course, only if the user should so wish) to help it clarify and confirm a verdict.
For example, if System Watcher suspects something, it establishes the chain of events, and finds the ultimate malefactor (from which everything began). At that moment it asks the cloud, “do you know anything about this shady character?”, and the cloud answers, “You know what, I’ve long suspected this dodgy specimen, and, since you’ve asked, I reckon you’ve pretty much confirmed that my suspicions were right all along, and this is indeed a most bogus beastie,” after which System Watcher delivers the verdict and gets down to cleaning up the mess.
Then you could say that all the fuss is just about signature patterns – same old, same old; nothing new here. But not all signatures are born equal. Standard signatures contain specific descriptions of malware, but BSS patterns contain actions of programs. The former are infinite in number; the latter are very limited in number. The advantages are manifest in terms of detection.
Of course here we’re going down a well-trodden path – just more effectively – but we are still trying to do one thing: root out the bad stuff. Besides, this is just one of the useful features we use in our fight against malware.
The theme for the next post will be whitelisting – a service for checking reputations against trusted programs and websites. This is an approach that’s just the opposite of the traditional one: we don’t try to detect the bad stuff – just all the good stuff. In this case the bad stuff can relax for once!
Thank you everyone for your attention!
You can read more details about System Watcher here.