September 25, 2018
Cyber-tales from the dark – and light – sides.
Hi folks!
Today I’ve got some fresh, surprising cybersecurity news items for you. The first few are worrying stories about threats stemming from a certain ubiquitous small device, which many folks simply can’t be without just for one minute – including in bed and in the bathroom. The last few are positive, encouraging stories – about women on the up in IT. Ok, let’s dive in with those worrying ones first…
Don’t join the Asacub victim club
These days, folks tend to entrust their (trusty?) smartphones with all sorts of stuff – banking, important work and personal documents, messaging (often with very personal details strictly for a few eyes only), and more. But, hey, you’ll know all this perfectly well already, and may be one of these folks to this or that extent yourself; and if you are – you really do need to read this one carefully…
At the end of August a sharp increase was detected in the proliferation of the Android Trojan Asacub, which exploits that peculiarly human weakness called curiosity. The Trojan sends a text message with words like: ‘Hey John: You should be ashamed of yourself! [link]’, or ‘John – you’ve been sent an MMS from Pete: [link]’. So John scratches his head, becomes as curious as a cat, wonders what’s in the photo, clicks on the link, and (willingly!) downloads an application… which then proceeds to stealthily access his full contact list and start sending out similar messages to all his peers.
But this crafty malware doesn’t stop there. It can also, for example, read incoming texts and send their contents to the hackers running the malware, or send messages with a given text to a given number. And the ability to intercept and send texts gives the authors of the Trojan the ability to, among other things, transfer to themselves funds from the bank card of the victim if the card is digitally connected to the phone number. And as if that weren’t bad enough – there’s a bonus for the victim: a huge bill from his mobile provider for sending all those messages to everybody.
So how can you protect yourself from such fearsome mobile malware? Here’s how:
- Don’t click on suspicious links;
- Carefully check which rights are being requested by the downloaded application (e.g., microphone, camera, location…);
- And last and most: the simplest step – install reliable protection on your Android smartphone.
Android? Hmmm. I can hear all the sighs of relief just now: ‘Aaaaahhhh, thank goodness I’ve got an iPhone!’!
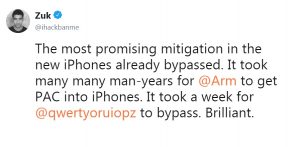
Hold your horses all you Apple lovers; here’s a couple of links for you too (don’t worry: you can click these – honest!):
Ocean’s (Model) 3
As if Tesla and his dope-smoking owner aren’t in the news enough…
This one’s straight outta Gone in 60 Seconds.
A car thief goes up to a new Model 3 in a car rental parking lot, unlocks it as if it belongs to him, and off he drives. To carry out the theft he needed just one item. Can you guess which? Yep, that (untrusty) cell phone again!
The thief had called up Tesla support and asked them to add the car’s ID number to the account of his mobile app – which they did! Before speeding off, the thief turned off the vehicle’s GPS so it couldn’t be tracked. What he didn’t think of though was that he’d need to fuel up at a Supercharger – and that’s how he was caught: the owner of the stolen car gave the cops the location of the (connected, of course) Supercharger used – and in they swooped.
And there we have it: yet another tale from the infinitely unsecure Internet of Things. I don’t want to say it again as I’ve said it far too many times already, but… ok… er… I will: please, world, wake up! The IoT needs securing – fast! As fast as a Tesla Model 3!
Pegasus sussed
The other day a detailed investigation was published on Pegasus – a commercial spy app for mobile phones developed by the Israeli company NSO Group. We’ve already written about different variations of this app, more often than not sold as a parental control app, but which differs little from espionage malware.
So what can Pegasus do? It can steal text messages, call histories and recordings of conversations; track the phone via its GPS functionality; steal data from the browser – including the history of visited sites; download photos and videos from the phone, and look through the contacts. An impressive list for ‘parental control’, no?
Pegasus can also use the phone’s microphone to record sounds around the telephone; it can take photos and look through the calendar and notes; and it has the function of backdoor to access social networks and messengers. The app has been found to be used in a full 45 countries. And of course it can be used not only for keeping tabs on unfaithful spouses and wayward teenagers. Judging by the particular countries the investigation has shown up as where the app is being used, it looks quite possible that it could be used for political/state snooping.
KL: the logical target
A curious theory was recently put forward about the root cause of the false allegations against us by a handful of US media outlets: our protection does its job properly – uncovering and securing against the dark cyber-shenanigans of various intelligence agencies around the world. And this version is often backed up in leaks, like Vault 7, which show similar dissatisfaction with our products on behalf of the same intelligence agencies. Yes, I think it’s quite logical that this could indeed be one of the reasons we’re targeted. After all, we, on principle, detect any malware no matter where it may come from or what its purpose may be – because malware is malware. What do you think?
But I want to finish on a lighter, more positive note…
Women in IT
Recently I saw a news item about a Victoria’s Secret model who knows how to code. And folks were all kinda shocked, as if it was something unusual! But I know many clever and beautiful female computer programmers who catch cybercriminals as well as anyone. In our R&D, btw, we have working twice as many women than the norm for the cybersecurity industry. And our renowned GReAT team isn’t an exception – as Noushin Shabab told us not long ago. And should Lindsay Scott tire of modelling and want a stable job in IT, send us your resume!
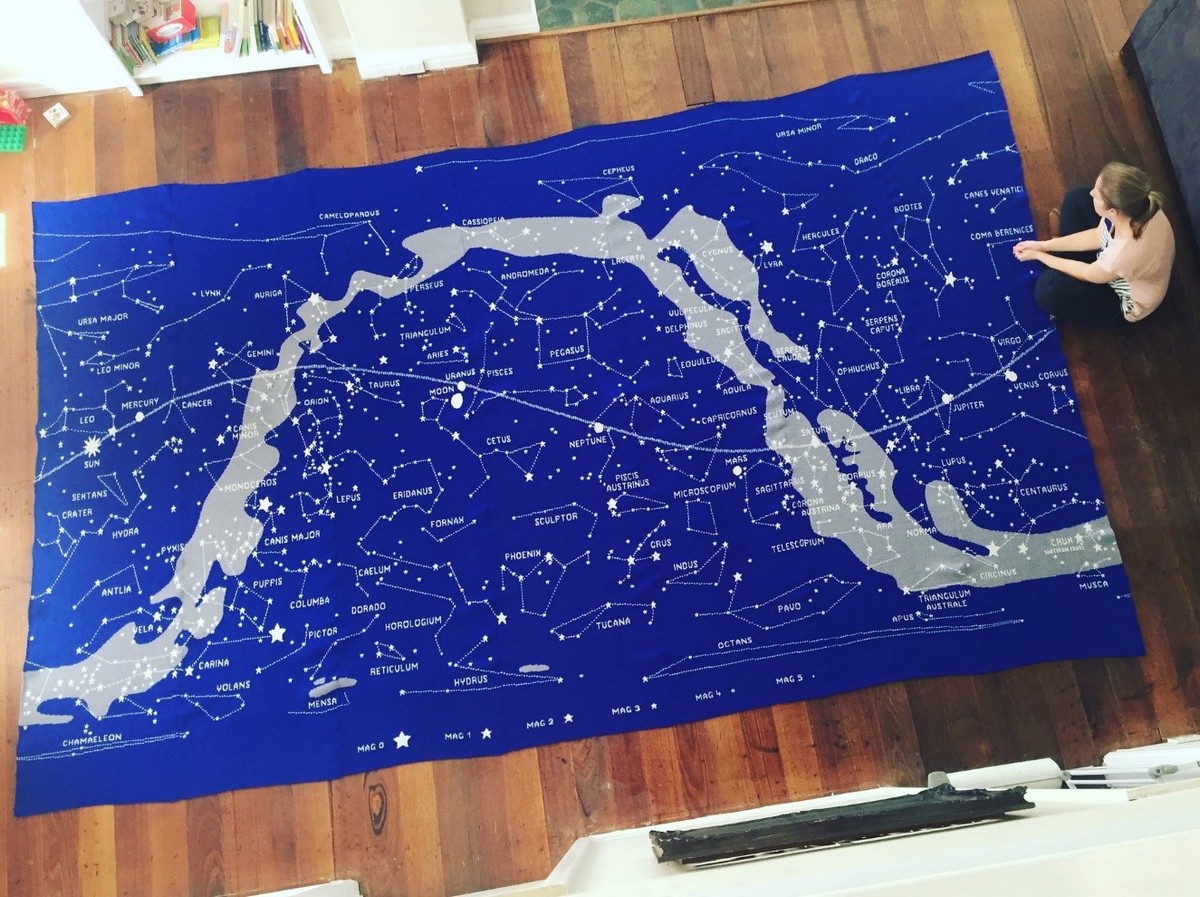
Lastly – also on the topic of talented women in IT: Here’s the story of an Australian woman who hacked a… knitting machine to make large tapestries with massive equatorial star maps on them! Like!