February 6, 2014
AVZ: Heuristics without false positives to combat future threats.
How can you locate and destroy ALL the maliciousness hiding in the sleeping jungles of your computer?
In particular, the extra nasty maliciousness that’s never ever been seen before, which also happens to have a mega-high malevolent-IQ (and is often state sponsored)?
Easy. The answer’s simple: you can’t.
Well, you can at least have a good go at it; but to find the proverbial black malware cat in a pitch black room you need a handful of top-notch pros to do the task manually: expensive. But to do it automatically with a boxed antivirus product – that’s a whole different matter altogether: you normally just get as far as getting on to the scent of super sophisticated infections, but that’s about it. That is, at least, using the old-school AV approach that uses classic antivirus signatures and file scanners.
So what’s the solution?
Again, simple: put some mega brains to hard work – to automate sophisticated-infection seek-and-destroy functions in an AV product.
So how we do that?
By getting those mega brains working on the systematic intellectual development of protection by analyzing signals from dozens of KL sensors placed all over the protected computer. Such an omniscient systemic analysis is so much more effective than the AV equivalent of fortune-telling from coffee grounds. Better a practical approach to proactive protection than guesswork, no? Yes.
So, these sensors… One feature that’s found in practically all of them is KL’s custom weapon of choice: heuristic analysis.
Turns out heuristics in computer virology have been around for 25 years or so already. Some AV companies dropped this tech as it requires constant development, while others minimized its use or just froze it. Still, in case heuristics’ significance passed you by, here’s briefly what they’re all about…
Malicious code can be identified in two ways – either directly or indirectly:
Directly – this is all about classical signatures: we know what a malware code looks like, so we develop a signature for it and search for it when scanning a suspicious object.
Indirectly – this is what heuristics is all about. We can reveal maliciousness based on previous knowledge of typical sequences of commands in code or of metadata (static analysis), or on behavior (dynamic analysis).
Example of indirectly: a program writes itself into the autorun key of the system registry, intercepts keystrokes, opens a port and transmits something via the Internet. Also, the program writes some kind of data to the hard drive in cylinder 0, head 0, sector 1 – i.e., modifies the MBR (master boot record). Let’s face it, this kind of behavior… it hardly comes across as that of an innocently benign program does it?
Now, the key advantage in using heuristics over signatures is that we don’t need to know what a bit of malware ‘looks like’, i.e., we don’t need to know its unique code. Instead, we carpet bomb the whole spectrum of maliciousness (including of the unknown kind) by analyzing specific malicious actions and behaviors.
However, it turns out that the variety of these actions and behaviors is much much less than the number of possible malware code combinations . For example, with just one heuristic record we detect around 600,000 variants of the WBNA worm! So you can imagine just how much good heuristics can speed up a virus scan (bypassing a need for 600,000 separate records!).
Heuristics are used in practically all our protection modules (for example, the deblocker, anti-rookit and anti-phishing modules). They help high level analytical technologies like System Watcher and cloud-based reputational services to better understand a comp’s inner environment and uncover the most cunning of attacks. Besides, there’s our special AVZ module for automatic heuristic analysis of a system. On this I need to go into a little more detail here…
AVZ was introduced in full combat mode as far back as 2007. It plays rather a lot of different roles (shredder, backup, trash clean-up, file integrity checker, system restore wizards) depending on the product it finds itself in. But from the point of view of heuristics and protection from unknown threats it does two main things – (i) enables (human) technical support for remote diagnostics and curing particularly stubborn and difficult infections; and (ii) provides a set of tools to enable experienced users and sysadmins to identify malicious anomalies themselves on the comps and networks they manage.
The most important feature of AVZ is its own heuristic analyzer (updated every day), which makes a real good job of keeping track of everything that’s going on inside a computer. And that’s half the job done already! AVZ interprets different parameters and makes it possible to pinpoint maliciousness, analyze the system, and use the results to create a quarantine zone with suspicious objects and a detailed report on all files.
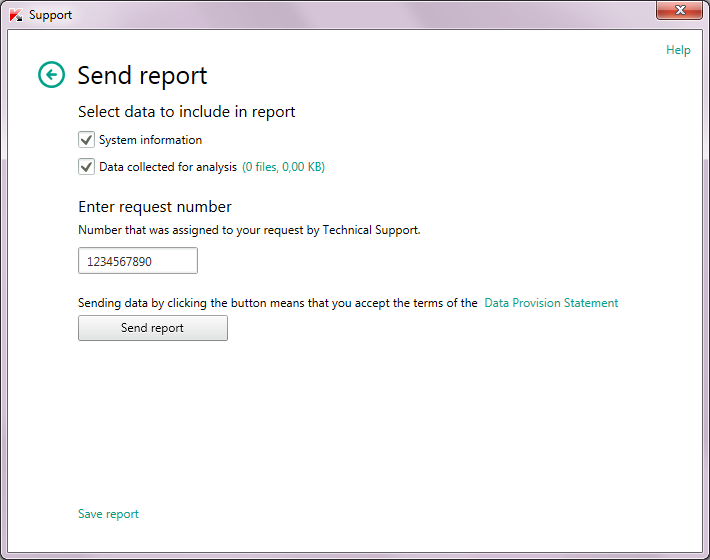
The great thing about this report is it’s equally suitable for being read by both a (human) expert and… a robot! Having analyzed it, our tech-support can accurately diagnose and prescribe treatment; while a robot after automatically analyzing it can create a remedy for launching on an integrated script interpreter.
Yep, we have a special script language interpreter inside our products, which we created from scratch and fine-tuned specifically for computer virology tasks. It contains all the instruments needed for AV surgery (deleting files, placing objects into quarantine, registry clean-up, terminating processes, and so on), together with other helpful technologies (deferred deletion, combating active infections during treatment, and so on).
One neat feature of the report is that it contains only really critically important information about the system for antivirus diagnostics. Objects that are for sure sweet and innocent are automatically whitelisted so as to not get in the specialists’ way and to expedite the analysis.
Then it’s all a matter of technique: the script remedy is delivered to the injured computer and takes restorative measures. The user just needs to copy the text into the window of the script. Experience shows that this is an irreplaceable feature both upon installation of protection on an already infected system (including by unknown threats), and when correcting the aftereffects of an infection.
Any heuristic analyzer has limitations when it comes to false positives. This is logical, as heuristic analysis works with assumptions about the maliciousness of an object based on past experience – not facts. Thorough testing and whitelisting have a good go at compensating for this, but all the same there still occur some errors. Alas, the tech hasn’t been invented yet that could sort this totally once and for all… but we’re working on it :). Meantime, the main thing is to fix errors ASAP and issue correcting updates ASAP. However, with AVZ… there’s no such problem!!
First, AVZ works all on its own, and doesn’t pester the user with tech-savvy questions and alerts. The results of the work of the module are only seen by the tech support expert that receives it. Or the robot :). Second, both the expert and robot are able to eliminate false positives themselves! Yes, you read that right – really! Upon every scan of new data they can manually or automatically (respectively) reveal the false positives and ineffective records and make changes accordingly!
Who said the tech hasn’t been invented yet?