May 23, 2018
Weightlessness, ver. 2018.
From time to time I find some planned OMG moments in my diary in among the unscheduled ones. This short post is about my most recent one…
NOTES, COMMENT AND BUZZ FROM EUGENE KASPERSKY – OFFICIAL BLOG
May 23, 2018
From time to time I find some planned OMG moments in my diary in among the unscheduled ones. This short post is about my most recent one…
May 22, 2018
Having strolled about Longyearbyen, it was time for the next leg on our mission to the North Pole – to get to Barneo ice camp. Here, much like in Longyearbyen, things weren’t quite so extreme and harsh as might be expected. The only issue for first-timers could be a queasy feeling in one’s lower abdomen – perhaps caused by butterflies.
May 17, 2018
Hi folks!
Ok, you’ve had your fun and games, now for some detail on my recent North Pole trip…
Now, unlike some, I wasn’t skiing to the North Pole. I consider myself sporty and adventurous… but I know my limits ). No, I was going the lazy man’s route:
Oslo > Longyearbyen, Svalbard > Barneo (on an An-74) > North Pole (in a chopper).
Ok, so where shall I start? Since we didn’t have much time at all in Oslo, I’ll start in Longyearbyen (the ‘Longyear Town’!).
We arrived there on a scheduled commercial flight from the Norwegian capital. There are several of these per week (there are also charter flights sometimes), but the exact number can change due to cancelations, in turn due to the extreme weather conditions. We were lucky – our flight was on schedule.
May 17, 2018
Hi folks!
As promised, herewith, my answers to Thursday’s polar quiz questions:
Ok, first – my answers to those four non-visual questions:
Question 1: How do you get to the North Pole?
Answer A: The simplest and cheapest method:
Buy a plane ticket from Dubai to Seattle or San Francisco. These routes fly real close to the Geographic North Pole. I believe the route Anchorage-Frankfurt (on Condor) also still does too (I flew it back in 2013, but I was sleeping around the time of the near-polar-flyover). While back in the mid-nineties there was a direct Aeroflot flight between Moscow and San Francisco, and they even gave out ‘flown over the North Pole’ certificates!
Answer B: Another, more expensive, way of getting to the North Pole – this time actually right to it, up close and personal freezing – is on one of the regular expeditions organized by the Russian company VICAAR.
Those two gents in the above pic are Victor Boyarskiy and Leonid Plenkin, who escort you up to the North Pole if you decide to go with VICAAR. Btw, that photo was taken in an Antonov An-74, en route from Svalbard to Barneo; from Barneo to the North Pole you take a helicopter.
May 10, 2018
Hi Folks!
As promised, herewith, a rewind back to all things polar… – but with a twist. It’s not a full-on description of what I was doing recently up at the North Pole, or why; that, I’m sure (if I do ever get some free time, finally!), will come later.
No, this post is a bit of fun. Why fun? Because I’ve been on the road for three weeks now, visited 10 counties/territories in the process, and think I – and by extension you – need a little fun. (And I need to get home fast too to recharge my batteries, catch up on sleep, and lower the levels of adrenaline in the bloodstream.)
So, fun?…
Yes: for this here post is a quiz. Just that in itself is a twist (since when has a whole post of mine been nothing but a quiz?). But there’s more twistiness: it’s a purely visual quiz – as in, all questions relate to photographs (taken be me). No wordy brainteasers.
Ok, now, the word in bold above gives the game away to some extent as to what these pics are of (and, thus – what this quiz is about), but, and here’s even more twistiness: it just so happens that this quiz, based on these pics, isn’t just about the North Pole. It’s also about the South Pole, since, handily, I’ve been to both. And since I don’t know many folks who have been to both the top and the bottom of the world – and in fact none who are also photography freaks like me – well, I thought I’d capitalize on this rare lucky combination and have a bit of fun with it. Crikey, that’s a long intro to explain just what this post is about!
Ok, long explanation over, let me put it another, laconic, way: this is a visual quiz where you have to work out where all the following pics are taken: near the North Pole in the Arctic, or near the South Pole in Antarctica. That’s it! (What could be simpler?:)
Oops, nearly forgot: there are four non-visual questions in this quiz too. They are:
I’ve quite a few different answers to those four (they’ll come in a later post), but I’m just curious as to what you might come up with. Maybe your answers would be way cooler than mine?
Anyway, without much more of ado, let’s get this polar quiz started:
Btw: you won’t believe how far those mountains in the background on both pics are. Ok, you can guess those distances too ).
May 8, 2018
Hi boys and girls!
Been a while, I know, but I’m back – and with loads of on-the-road tales to recount that have piled up…
Right now I’m in Terminal 5 of Heathrow Airport, which is fitting: I’ve seen a lot of airport terminals just recently, but I haven’t had enough time in the departures lounges to keep up with events as they’ve been happening – as they’ve been happening so fast and furious and frequently and non-stop. I’ll at least make a start with some catch-up here…
I really should start where this recent spot of globetrotting began a few weeks ago – heading to the North Pole! But… Since I still don’t see much free time on the horizon for extensive travelogue writing and photo editing, I’ll settle for just this one interim post for now to keep things bobbing along on this here blog, and it will have to be a relatively brief one (I’ll do the proper catch-up a bit later once I get home). It’s one about some mind-boggling contrasts I’ve seen over the last few days…
Now, returning from one of the earth’s poles back to civilization is always a bit lot of a shock to the senses. From a place where there is literally nothing but cold, ice, snow and blue sky, to a place where there is warmth, no snow or ice; supermarkets, roads, pubs, offices, Wi-Fi, drinkable tap water and all the rest of civilization’s better features… well, you get the picture: it’s always going to blow the mind a touch and take some time to acclimatize…
April 28, 2018
April 26: significant for you? Perhaps it’s your birthday? If not, I bet you’re a patent lawyer, or someone who works with patent lawyers. For April 26 is World Intellectual Property Day! Accordingly, yesterday I congratulated all those connected with this tricky profession, and wished them every success within it.
Actually, not all those connected with this profession. Not patent trolls, and not legal white-collar ‘consumer champions’. I wish them… you can imagine.
But back to the positive…
Hearty congratulations to all the KLers in our IP protection department (that’s dozens of headstrong specialists with unique expertise, led by the uniquely headstrong N.K). Hip, hip hooray!

So, on this special occasion, we decided to do a mini-retrospective – to look back over how our IP department developed, and to then look to the future to forecast how it’s going to further develop.
April 23, 2018
Throughout human history there have been many interesting moments and fascinating stories. Out of all of them, I reckon one of the most amazing is the story about how homo sapiens settled on remote islands across the Pacific.
Around two or three thousand years ago, from the shores of what is today Papua New Guinea, they sailed in the simplest and tiniest of boats, generation after generation, century after century, to populate island after island, apparently even reaching the shores of South America – 15,000 kilometers away!
Archeological research of this great eastward emigration is a little unconvincing so far, and anyway, surely many of the traces of mankind from back then will have been washed away or submerged under the rising ocean levels and lost forever. However – hurray for the geneticists! – modern-day investigations scientific alchemy now give us a detailed picture of the timing and direction of the two main branches of the eastward exodus and building up of the populations of Oceania.
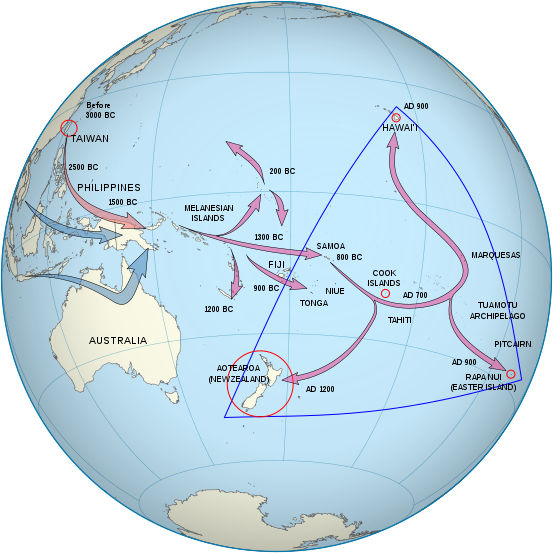
The first wave of migration (a quick glance at trusty old Wikipedia tells me) took place some 30 to 50 thousand years ago from southeast Asia via modern-day Malaysia, Indonesia and Papua New Guinea, to Australia and the islands of Melanasia. Now, I’m no anthropologist, but something tells me that back then they probably didn’t need a boat to get to Vanuatu or even Fiji – they could have walked, or paddled ). The sea level was much lower then than it is today, and the ocean never gets that deep round these parts (as you can see on Google Maps) anyway. I reckon they didn’t make it further to Samoa as they weren’t sailors.
April 20, 2018
“When you tear out a man’s tongue, you are not proving him a liar, you’re only telling the world that you fear what he might say.”
Tyrion Lannister, Game of Thrones
Dear Mr. Dorsey and the rest of the senior management of Twitter,
I see that of late you’ve been having concerns about the ‘health’ of your social media platform, and how it can be used maliciously for spreading disinformation, creating social discord, and so on. As a long-time advocate of a safe and friendly internet, I share these concerns! Though I thought my company stood on the periphery of this social media storm, it turns out I was quite mistaken.
At the end of January of this year, Twitter unexpectedly informed us about an advertising ban on our official accounts where we announce new posts on our various blogs on cybersecurity (including, for example, Securelist and Kaspersky Daily) and inform users about new cyberthreats and what to do about them. In a short letter from an unnamed Twitter employee, we were told that our company “operates using a business model that inherently conflicts with acceptable Twitter Ads business practices.”
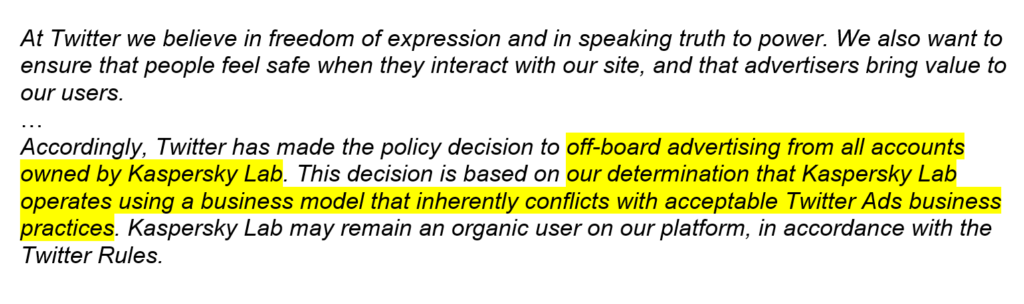
“OUR DETERMINATION THAT KASPERSKY LAB OPERATES USING A BUSINESS MODEL THAT INHERENTLY CONFLICTS WITH ACCEPTABLE TWITTER ADS BUSINESS PRACTICES”
Huh? I read this formulation again and again but still couldn’t for the life of me understand how it might relate to us. One thing I can say for sure is this: we haven’t violated any written – or unwritten – rules, and our business model is quite simply the same template business model that’s used throughout the whole cybersecurity industry: We provide users with products and services, and they pay us for them. What specific (or even non-specific) rules, standards and/or business practices we violated are not stated in the letter. In my view, the ban itself contradicts Twitter’s declared-as-adopted principle of freedom of expression. I’ll return to that point in a minute, but first let’s look at the others:
Read on: Common sense hasn’t died. It just appears to be having a gap year…
April 18, 2018