June 20, 2019
The St. Petersburg International Forum – despite problems, still awesome.
Hi folks!
As mentioned in my previous post, I was up early down in Sochi after the long toasts the night before, and heading to the airport. Next stop – St. Petersburg; specifically – its International Economic Forum, which I was attending for the first time.
For nearly a quarter of a century SPIEF has been impressing with its scale and the caliber of its participants. Official figures state the number of those taking part this year at more than 19,000 – coming from 145 countries of the world. And that includes CEOs of multinationals, and ministers and presidents of countries – all toing and froing and hobnobbing and speaking up on stages, often with their deputies and press services not far away.
So. SPIEF. Herewith, the plusses:
It’s really convenient: in a short time it’s possible give a presentation in among other heavyweight speakers, give a slew of interviews, and meet and chew the fat with whomever you need to or want to – all under one roof and within two or three days. Indeed, this is the whole reason for forums such as these. Also – St. Pete isn’t far for me, plus it’s always a pleasure having a stroll up and down Nevsky. In short – the plusses are very substantial plusses.
Now – the minuses:
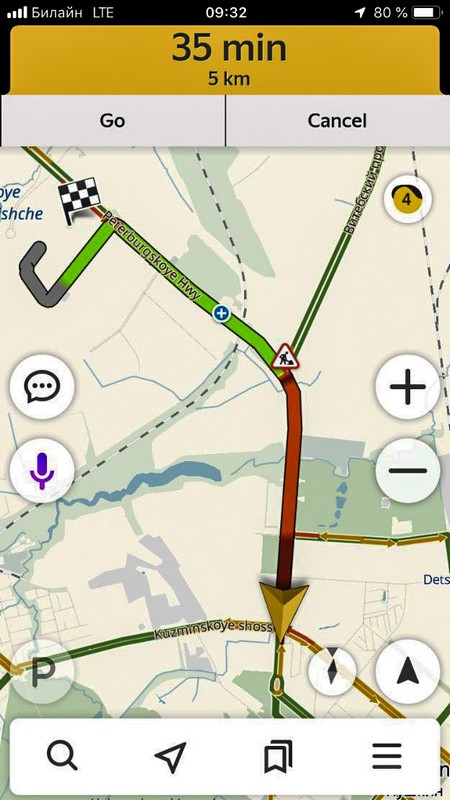
The traffic jams! Not that this is the forum’s fault, but still. From our hotel in Pushkin on the outskirts of the city to the ExpoForum Center it’s just a seven-kilometer drive (and you totally miss out downtown!), but every morning we were more than an hour getting there! First, because they reduced the width of the normally three-lane highway to just one lane; second, because the security checks at the entrance to the complex took so long; third, apparently, because there was a complete and utter – catastrophic – absence of any public transportation serving the event. Organizers: I hope you’re reading. In three words: ‘GET A GRIP’! Don’t let such basic logistics matters spoil an otherwise excellent event!
Wait – there are more minuses!…
The signage and guidance around the ExpoForum Center was idiotic. We twice ended up walking around in circles in trying to follow the signs to get from point A to point B – which were a mere 100 meters apart! Next, the line at lunch was so absurdly long I gave up waiting and went hungry. I don’t have time to waste like that! I’m sure the other participants don’t either. So, what, bring sandwiches next time? Looks like it, given such progressive organization of the catering arrangements.
Read on: The St. Petersburg International Forum – despite problems, still awesome.