Hi folks!
My April journeying continues. It’s already seen me visit such charming cities as Hanover, Baku and Dubai (reports thereon coming soon). Next stop – Singapore. The garden city, the island wonder – one of my fave cities on the planet, if not the fave. But oh it’s hot. And, oh, it’s humid. But it still remains the city of the future. Maybe that’s why I like it so much?…
First, a few ok pics (mine), and some really good pics (not mine; I still need practice) of this wonder-city – by day, by night, of the ships waiting in line for access to the port:
So why was I here (as if I needed a reason)? Because the annual Security Analyst Summit was being held here – the eleventh! And it was… hmmm – I’ll get to that in a bit…
First – how does one go about gauging the success of a SAS? How do you measure it? Was it totally awesome, or just so-so, or something else? Well, IMHO, you can tell if it was totally awesome if, afterward, you have a strange, somewhat paradoxical feeling: on the one hand you have nothing but positive emotions – a euphoric aftershock that just won’t go away. On the other – you’re already aware that something’s sadly lacking in your life, and will stay lacking for another year – the buzz of a SAS! And on the other – third?! – hand, you feel a little… afraid – when you wonder just how on earth next year’s event will be made even better than this year’s! But then you remember how every year after a SAS you think the same thing – and the following year’s event does turn out even better, and you start to feel better again. All these psychological symptoms together should really be called ‘post-event syndrome’. Must remember that term for next time…
Oops. I’ve digressed. Let me get back to ‘was it good?’. It was, as I hope the previous paragraph indicates. But also – have a look at all the comments, links, likes…
If you’re a new reader here, and maybe SAS is new to you too, briefly, SAS is: an annual event bringing together experts (and the press, bloggers) from all over the world to basically talk to each other, in an informal setting, all about cybersecurity. Announcements, presentations, achievements, challenges, industrial CTF, etc., etc. For a bit more on the SAS template, go here.
Next up: where, why, how, who, from where…
SAS-2019 brought on a ferocious bout of post-event syndrome, whose intensity was all the more acute due to fears that some folks might pull out due to geopolitical reasons. But in the cybersecurity industry folks think with their heads and aren’t swayed by sensational headlines. After all, battling the cyber-baddies is only effective when done together, exchanging information, and telling each other about our victories over the computer underground. Cybercriminals know no borders. And the cyber-goodies shouldn’t be limited by them either. And I’m so glad that our colleagues and competitors in the industry feel the same way.
So, there we were fearing no-shows, but in the end not only did everyone turn up but even more did than we expected! But that figures really – for who doesn’t want to get better acquainted with the company that’s being targeted because it takes a principled stand on protecting users from any cyber-vermin, no matter who may be responsible for it and no matter how much it roils certain very powerful cyberwar-mongers. SAS-2019 broke all its own records: 500+ guests, 100+ contributors, 34 countries represented, ~70 presentations, ~10 workshops and training sessions, and more coverage on social media and in the press than ever before.
Right, where did it all start this year. Ah yes, like every year – it all starts actually months in advance when a countdown clock starts showing the number of days, hours and minutes there are left until the event. Fast forward to the morning of the first day, and those clocks have just minutes left, and the anticipation is hitting fever pitch… All the kit and chairs are in place, microphones fully charged, lighting and visual effects all set up, cameras ready (prepare to flash)…
One minute left…

And we’re off!
After a short welcoming speech, I was pinged to get up on the stage. Of course I obliged, gave a very warm warm-up speech, and also took some pics of the audience from the stage. Why should the audience have all the happy-snapping fun, eh? )

After me it was expert after expert sharing their stories – each one fascinating…
This year the number of presentations was the highest it’s been, as mentioned above, but the diversity of types of presentations was real wide too: some were very technical; others were more business-oriented; there were special training sessions on reverse engineering and other methods for pursuing the cyber-swine; a mini-exhibition; an open presentation room for rooky specialists, and a new feature called SAS Unplugged… As to the best of the best content – that will be coming up shortly in a separate cyber-news-from-the-dark-side post.
This year’s SAS brought us for the first time the following:
- Separate cybersecurity white-hat hacking streams;
- A small exhibition of participating companies;
- Industrial topics;
- Lots of other stuff, but I can’t quite remember it all.
Come the evening, though everyone was no doubt tired trying to take in all the new information of the day, we all headed to a super seafood restaurant I always visit when in town. Yeh! Yum!
And that was that – almost. Time left only for the final few mega-presentations that are traditionally saved till last. They really were something. If interested – have a search for them on the internet.
Then it was my turn again up on stage. ‘Thank you all for coming’, and the obligatory back-at-you pic:

PS: A big thank-you to Roman Rudakov. His ‘masterpiece button’ provided most of the photos in this post.
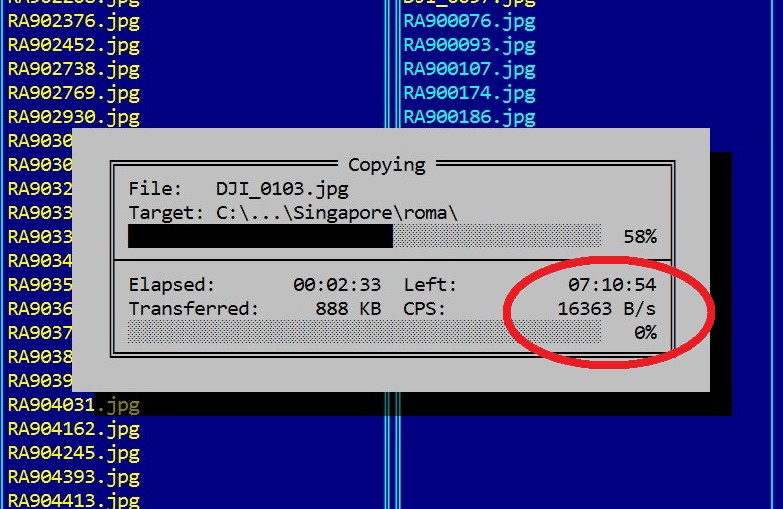
PPS: Briefly about where we held this year’s SAS – the Swissotel Stamford, where I’d stayed before, and which I only had negative recollections of. Not that I’m fussy when it comes to hotels. I’m comfortable up a mountainside in the cold and spending the night in a tent, but if a hotel says it’s a 5* hotel on the tin, I expect that’s what’s inside it too. Here, back in 2017 that wasn’t the case. However, this year I was very pleased with the place. Everything seemed to be in fully working order, everything seems to have been renovated, with everything shiny and new somehow. The one thing that they haven’t gotten round to is providing decent Wi-Fi, but that’s all:
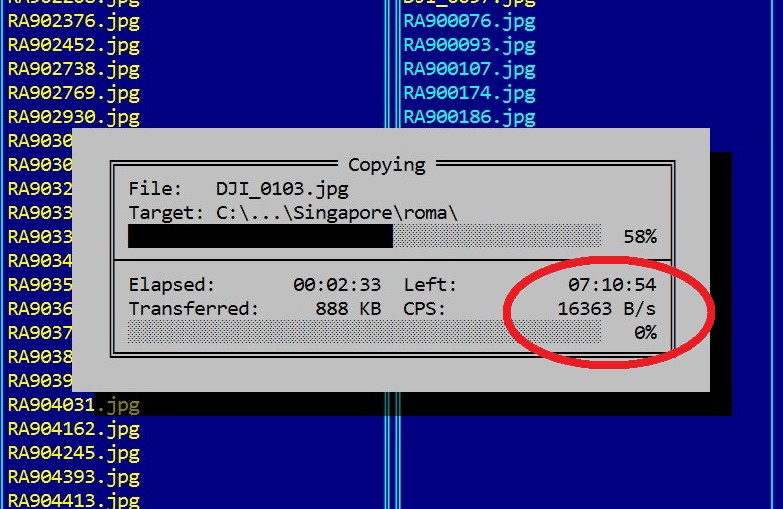
Yes, I know – I still use Far Manager! I’m used to it, that’s all ).
Well that’s it for today folks, but I’ll be back with more tomorrow…
All the pics form SAS-2109 are here.