Hi folks, or should that be – ho, ho, ho, folks? For some have said there is a faint resemblance… but I digress – already!
Of course, Christmas and New Year are upon us. Children have written their letters to Santa with their wish lists and assurances that they’ve been good boys and girls, and Rudolph & Co. are just about ready to do their bit for the logistical miracle that occurs one night toward the end of each year. But it’s not just the usual children’s presents Father Christmas and his reindeer will be delivering this year. They’ll also be giving out something that they’ve long been getting requests for: a new solution for fighting advanced cyberattacks – Kaspersky Sandbox! Let me tell you briefly about it…
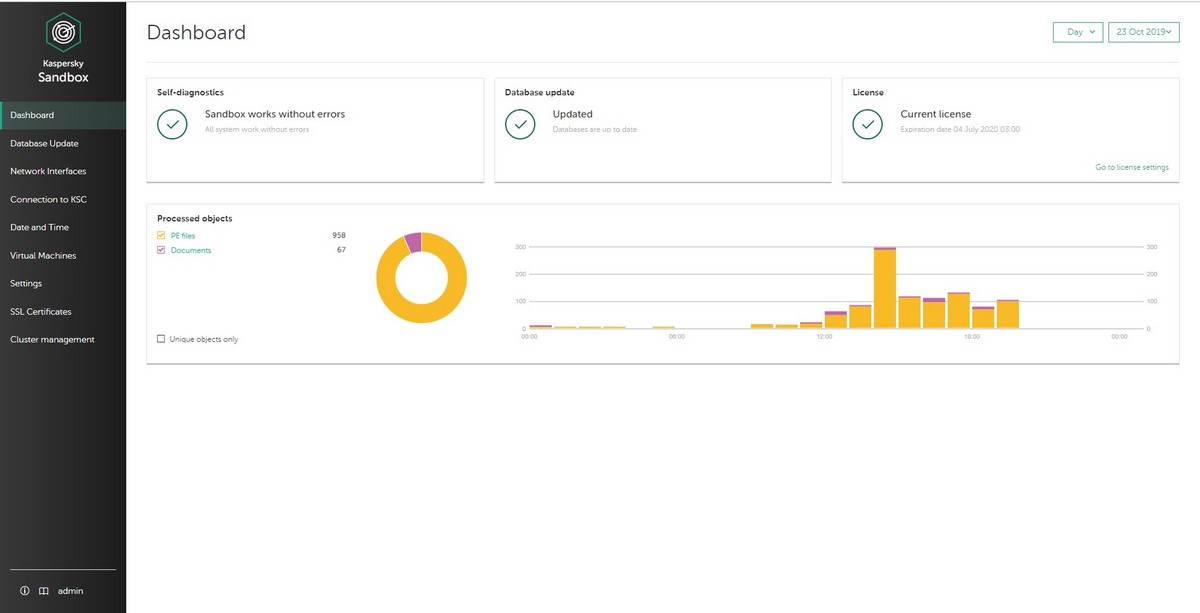
Basically it’s all about emulation. You know about emulation, right? I’ve described it quite a few times on these here blog pages before, most recently earlier this year. But, just in case: emulation is a method that encourages threats to reveal themselves: a file is run in a virtual environment that imitates a real computer environment. The behavior of a suspicious file is studied in a ‘sandbox’ with a magnifying glass, Sherlock-style, and upon finding unusual (= dangerous) actions the object is isolated so it does no more harm and so it can be studied more closely.
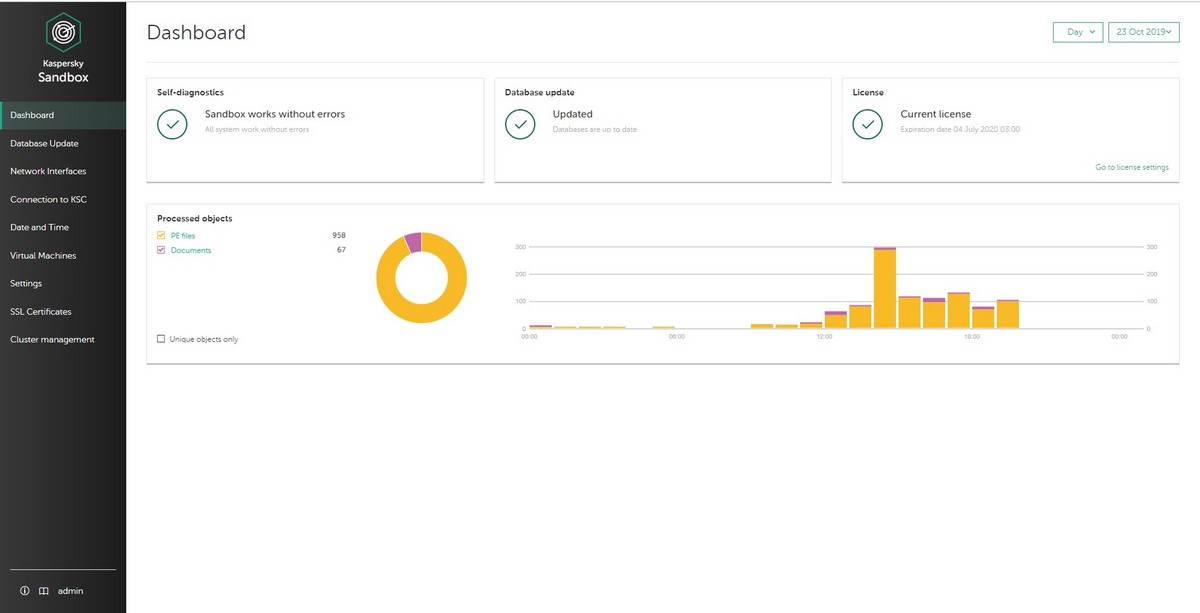
Analyzing suspicious files in a virtual environment isn’t new technology. We’ve been using it for our internal research and in our large enterprise projects for years (I first wrote about it on this here blog in 2012). But it was always tricky, toilsome work, requiring constant adjustment of the templates of dangerous behaviors, optimization, etc. But we kept on with it, as it was – and still is – so crucial to our work. And this summer, finally, after all these years, we got a patent for the technology of creating the ideal environment for a virtual machine for conducting quick, deep analysis of suspicious objects. And a few months ago I told you here that we learned how to crack this thanks to new technologies.
It was these technologies that helped us launch the sandbox as a separate product, which can now be used direct in the infrastructure of even small companies; moreover, to do so, an organization doesn’t need to have an IT department. The sandbox will carefully and automatically sift the wheat from the chaff – rather, from cyberattacks of all stripes: crypto-malware, zero-day exploits, and all sorts of other maliciousness – and without needing a human analyst!
So who will really find this valuable? First: smaller companies with no IT dept.; second: large companies with many branches in different cities that don’t have their own IT department; third: large companies whose cybersecurity folks are busy with more critical tasks.
To summarize, what the Sandbox does is the following:
- Speedy processing of suspicious objects;
- Lowering load on servers;
- Increasing the speed and effectiveness of reactions to cyberthreats;
- As a consequence of (i)–(iii) – helping out the bottom line!
So what we have is a useful product safeguarding the digital peace-of-mind of our favorite clients!
PS: And the children who behave and listen to their parents will of course be writing letters to Santa toward the end of 2020, too. Sure, they’ll be getting their usual toys and consoles and gadgets. But they’ll also be getting plenty of brand-new super-duper K-tech too. You have more word for it!…
Yours sincerely,
Father Christmas