February 20, 2012
Woodpecker Summit 2012.
The main occasion of our recent series of events in Cancun was the Security Analyst Summit (SAS) – the supreme congress of KL’s most distinguished virus analysts (woodpeckers; why woodpeckers? – see the full story here) and invited external security experts, who come together to boast about their achievements; exchange ideas, opinions and experiences; and, of course, do some informal networking.
The idea of the woodpecker summit goes back years. Its inception came in 1997 in Prague. We decided to reject the status quo – the usual boring model of what a summit should be about – and rethink the whole idea from scratch. What we came up with was a mostly informal get-together in comfortable surroundings in a distant, original location to discuss our technological breakthroughs. And one such breakthrough happens to have been the basic blueprint of our antivirus engine – named after the Czech capital where it was ‘born’. Clearly something was working with the summit format.
There followed rather a long break, but then in the early 2000s the tradition was kick-started again and these micro-conferences (in which only our employees took part at first) started being held sometimes several times a year. Since then there’ve been 15 of them.
Then in 2009 this tradition was updated and expanded – to version 2.0: transformed into much bigger, non-KL-exclusive, annual “woodpecker summits” in warm climes and with a serious intention to make the summits the main yearly event of the industry. Our latest – the fourth – was in the sunny Mexican resort of Cancun – coming across, I think, as a serious pronouncement of our present status. We had some 100+ attendees from 14 countries, great presentations and plenty of awesome team building. More details are in the guest post below from our Senior Virus Analyst, Yury Namestnikov:
—-8<----
Today I would like to tell you about an event called Security Analyst Summit. This is a recent conference organized by Kaspersky Lab for the fourth time… or for the fifteenth time – depends on how you count. The ever-present perk of the conference is networking of computer security experts in an informal setting: not just dressed casually, but in aloha shirts, shorts, and beach sandals. This year, we decided to hold the event in winter and there was a problem with beach sandals because nobody wanted to give them up. That’s why we decided to move closer to the equator and chose the Yucatan Peninsula. By the way, this is where those very Indians with a vulnerable calendar lived once: this December saw a buffer overflow, but the universe didn’t come crashing down and even didn’t even freeze, which is a good thing.
Boss giving a welcoming speech on the edge of a fountain
When we arrived, we were greeted by a sky-blue sea, white sparking sand, an air conditioned conference room, and three conference days. You can see that it was not easy to choose attendees ready to work in these inhumane conditions. This year, we had experts from a dozen of companies, including Adobe, Boeing, CrySyS Lab (the guys who discovered Duqu), Kaspersky Lab (there was no way we would miss it ;)), Microsoft, Team Cymru, cybercops from Interpol, Germany, Holland, Romania, and independent researchers.
Conference room with the attendees. By the way, many were tweeting: look out for #SAS2012
This is the fourth time we have invited outsiders to attend the conference: in addition to KL, this year, Adobe, Barracuda, and ThreatPost were sponsors. There is a steadily growing interest in the conference and I hope that in the near future it will grow to be one of the Industry Events. To be honest, it already is: the level of speakers and presentations spoke for itself.
Now to the meat, the presentations. I’ll start with saying that they were much juicier than those presented at AVAR and VB, which recently got cheesy. Speeches were really interesting and really exciting, with real facts based on real research, incidents, and operations, as was the case with the cybercops. Speakers also had a lot of fun: at the end of each presentation, there was not only a storm of applause but also a shot of tequila followed by another shot after each section. Those who moderated long sessions had the most difficult job to do but we chose the most well-trained ones, whose will was strengthened by the previous summits –
Plus, every speaker got a complimentary barrel of tequila to enjoy with a company of new friends in the evening. On the second day, when we had enough tequila barrels and could take some to the tables in front of the conference room, coffee breaks became even more cheerful:
Coffee break — Kaspersky style ;)
The most awesome presentations were from the Dutch cyberpolice: how they closed BredoLab, reckoned up and (what was the hardest) dug up evidence against its mastermind, how they fight child pornography on the Internet, presentations by Interpol about organizing Cyber Interpol (At last! Eugene has been talking everybody’s ears off about it for ten years).
Peter Zinn (Dutch police) answers questions
A team of independent researchers from the USA did an interesting research: they developed and carried out a test attack using a SCADA exploit, which provides full control over the entire control system of any jail, from the cell doors to perimeter protection. It turned out that Internet in jail is like a gopher: you can’t see it but it’s there! Naturally, these institutions do not allow any kind of Ethernet, let alone WiFi. However, time marches on and jails also get wired and critical PCs get finally connected to the net. And I will not tell you what the guards are doing at night sitting in front of these computers ;). By the way, the SCADA exploit was made for Siemens but there are no reasons not to do it for any other vendor. The research cost $2,500 – you must admit that this is not exactly a huge amount for those who want to get out of jail “early”.
What also comes to mind is reports about malware attacking POS terminals (the ones you can find in every store), treatment of legal websites (webmasters respond to messages about infected websites only 3% of the time), “the whole truth about Duqu”, identification of fake Facebook accounts, analysis of fresh APT, fight with exploits in Adobe, and malware by mail (literally, i.e. sent by snail mail :).
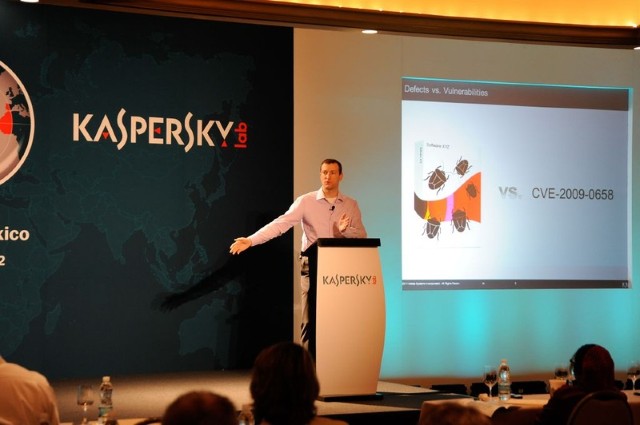
Brad Arkin from Adobe talking about bugs (obviously, big ones)
Levi Gundert form Team Cymru talking about the analysis of the 60 Gbit/s DDoS attack
Those who work a lot must have a lot of fun. New friends and the team spirit of those who fight viruses, Trojans, and their creators were tested in wild jungles and Maya pyramids on the third day. The general meeting resolved not to sacrifice anybody… Well, almost ;). Suddenly it turned out that the company employs different types of woodpeckers: flying, running, and even diving ones:
Some were talking shop even in the jungles
SAS has grown to become a useful, interesting, and (last but not least) very positive event. Yes, there were sometimes heated discussions among privacy advocates, experts, and cybercops, but the perfect atmosphere (and barrels with fire water) helped take the heat off and find common ground and the truth. The conference motto is “Let’s take the bull by the horns”, and it means that all interesting stories must be supported by action such as malware detection, website treatment, and capture of criminals. Till next year!
—–>8—–
So everything was just perfect and everybody enjoyed the event (me too!)
You can find more SAS 2012 photos here. Here and here are some nice pics from past SASes.