A few days ago Microsoft announced a large scale raid on the dynamic DNS service No-IP, as a result of which 22 of its domains were seized. The guys in Redmond said there were very good reasons for this: No-IP hosts all kinds of unpleasant malware; No-IP is a breeding ground of cybercriminals; No-IP is an epicenter for targeted attacks; and No-IP never agrees to working with anyone else on trying to root out all the badness.
Like in most conflicts, the sides have exchanged the contradictory volleys of announcements in the eternal tradition of ‘it’s his fault – no she started it’.
In particular, No-IP has said it’s a real goody-two-shoes and always willing to cooperate in eliminating sources of cyberattacks, while its clients are most displeased with the raid and consider it an illegal attack on legal business – since it’s possible to find malware practically anywhere, so interrupting services through a court is simply not on.
Is it legal to shut down a service because of #malware found?… When it can be found everywhere?…
In the meantime, the result of the raid has been rather far-reaching: more than four million sites were pulled, including both malicious and harmless ones – affecting 1.8 million users. Microsoft is trying to sieve the wheat from the chaff and get the clean sites back up and running; however, many users are still complaining about ongoing disruption.
To work out who’s to blame is a thankless and probably hopeless task. I’ll leave the journalistic investigations to… the journalists. Instead, here let me give you some food for thought: dry, raw facts and figures – so maybe/hopefully you’ll be able to come to your own conclusions about the legality and ethicality of MS’s actions, based on those facts and figures…
1) Shutting down 22 No-IP domains affected the operations of around 25% of the targeted attacks that we keep track of here at KL. That’s thousands of spy and cybercriminal operations ongoing for the last three years. Approximately a quarter of those have at least one command and control center (C&C) with this host. For example, hacker groups like the Syrian Electronic Army and Gaza Team use only No-IP, while Turla uses it for 90% of its hosts.
2) We can confirm that out of all large providers the No-IP dynamic DNS was the most unwilling to cooperate. For example, they ignored all our emails about a botnet sinkhole.
3) Our analysis of current malware shows that No-IP is often used by the cyberswine for botnet control centers. A simple search via the Virustotal scanning engine confirms this fact with a cold hard figure: a total of 4.5 million unique malware samples sprout from No-IP.
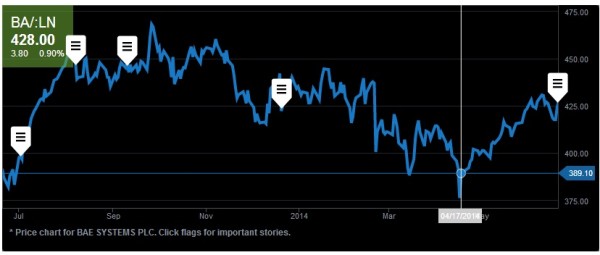
4) However, the latest numbers from our security cloud (KSN) show something not quite so cut and dry. Here’s a table showing detections of cyberattacks from dozens of the largest dynamic DNS services:
| Service |
% of malicious hosts |
Number of detections (in a week) |
| 000webhost.com |
89.47% |
18,163 |
| changeip.com |
39.47% |
89,742 |
| dnsdynamic.org |
37.04% |
756 |
| sitelutions.com |
36.84% |
199 |
| no-ip.com |
27.50% |
29,382 |
| dtdns.com |
17.65% |
14 |
| dyn.com |
11.51% |
2321 |
| smartdots.com |
0.00% |
0 |
| oray.com |
0.00% |
0 |
| dnserver.com |
0.00% |
0 |
So – No-IP isn’t leading in the number of detections, even though they’re still really high compared to most.
Here’s some more info for comparison: the % of malware hosts in the .com zone makes up 0.03% of the total; in the .ru zone – 0.39%; but in No-IP the figure’s 27.5%!
And now for other figures that add a bit of a different perspective: in one week, malware domains on No-IP generated around 30,000 detections, while in the same week on one of the most malicious domains in the .com zone, the figure was 429,000 – almost 14 times higher. Also: the tenth most infected domain in the .ru zone generated 146,000 detections – that is, about the same as the first ten providers of dynamic DNS mentioned above put together!
To summarize…
On the one hand, blocking popular services that are used by thousands – if not millions – of typical users: it ain’t right. On the other hand, closing spawning grounds for malware is right – and noble.
The takedown of No-IP domains. Was it right or wrong? Ambiguity with a big A
But then mathematics takes on the role of devil’s advocate, and proves:
Quantitatively, closing all the domains of No-IP is no more effective in combatting the distribution of malware than closing one single top malware domain in one of the popular zones, i.e., .com, .net, or even .ru. Simpler put, even if you were to shut down all providers of dynamic DNS – the Internet still wouldn’t become ‘cleaner’ enough to notice the difference.
So there you have it – ambiguity with a big A.
It leaves anyone in their right and honest-with-themselves mind to admit things are far from black and white here, and as regards the right and wrong, or good and bad, or Nietzsche’s thing – who can tell?
Still, another thought comes to mind at some point while reflecting on all this…
It’s further evidence that as soon as the quantity of piracy or degree of criminality gets above a certain threshold, the ‘powers that be’ get involved all of a sudden and start closing services, ignoring any notions of Internet freedom or freedom to do business. It’s just the way things are, a rule of life of human society: If it stinks, sooner or later it’ll get cleaned up.
The list of blocked services is already rather long: Napster, KaZaA, eMule, Pirate Bay and so on. Now No-IP‘s been added to the list.
Who’s next?
// Bitcoin? It’s already begun.
 I guess a sweater, jumper or sweatshirt on the singer just wouldn’t have been right :)
I guess a sweater, jumper or sweatshirt on the singer just wouldn’t have been right :)