October 10, 2013
K-LOVE & KISSES 2014: REASONS TO BE CHEERFUL, PART 3.
“The person needs to be brought round to the idea that he has to part with his money. He needs to be morally disarmed, and his proprietary instincts need to be stifled.”
No, not Don Draper; this is a quote of Ostap Bender, a classic fictional hero from 1930s Russian literature. And no, there’s no relation to the other famous Bender!
Thus, it would appear that, curiously, Mr. Bender knew a thing or two about capitalism, despite being from a Communist country. Hmmm…
Anyway, what he knew is that it’s sometimes possible to make folks part with their hard-earned shekels if they are manipulated the right way – the folks, that is.
Fast-forward to today… and we find this kind of manipulation alive and well – in a modern, hi-tech, cyber kinda way: Today, folks gladly hand over their Benjamins to the crims behind blockers, aka ransomware, an especially sneaky form of computer malevolence. But have no fear, KL users: in the new version of KIS, we’ve got a nice surprise waiting for the blocking blockheads and their blockers.
The principle and tech behind blockers/ransomware are rather simple.
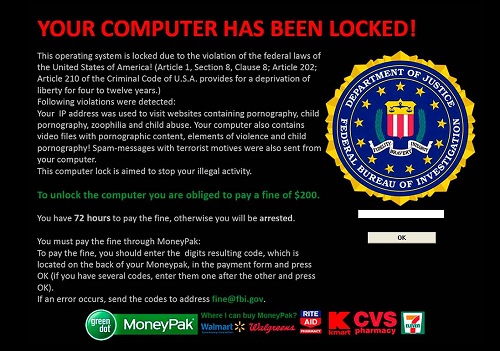
Using one of the various means available (for example, via a software vulnerability), a malicious program is sneaked into computer, which then displays an amusing (not) photo with scary (not – with KIS:) – text, and blocks the desktop and all other programs’ windows.
Unblocking is only possible (well, was possible – see below) by entering a unique code, which of course you can only get from the cyber-tricksters who infected the comp in the first place, and of course – for a fee, through premium SMS numbers or online payment systems. Until you pay the ransom, the comp remains kidnapped – no matter what you do (including Ctrl+Alt+Del), and no matter what programs you try to run (including antivirus); all you see is something like this:
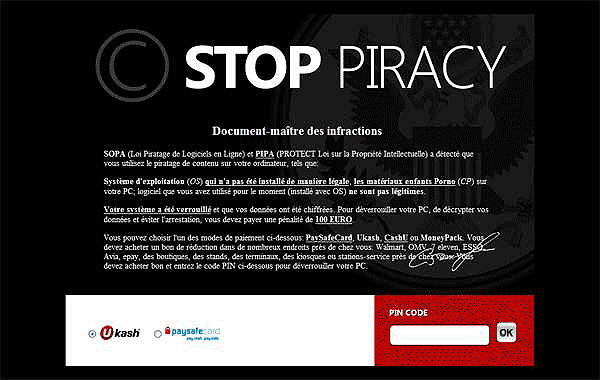
Or this (if you’re French):
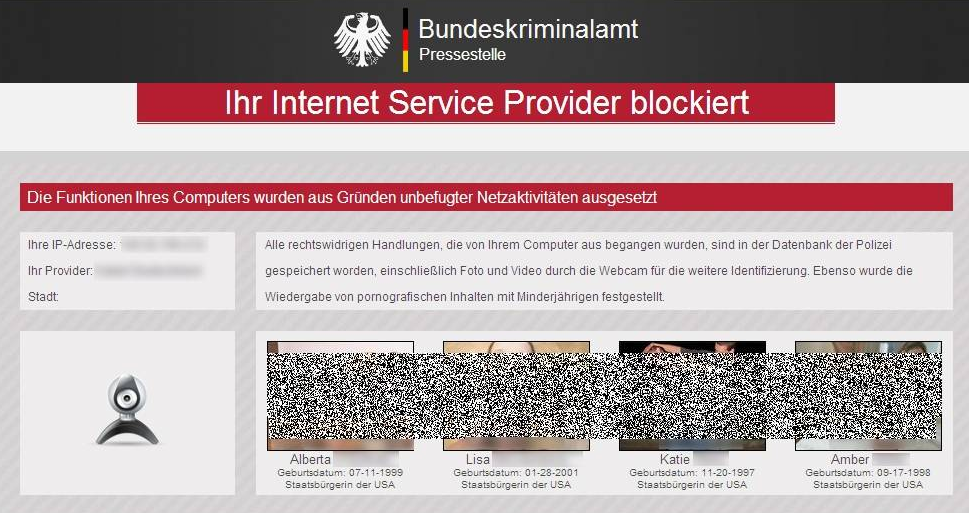
Or this (if you’re German):
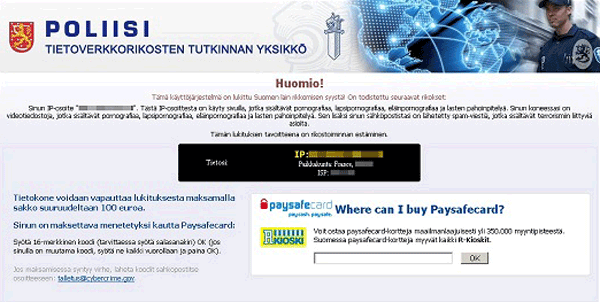
Or this (if you’re Finnish):
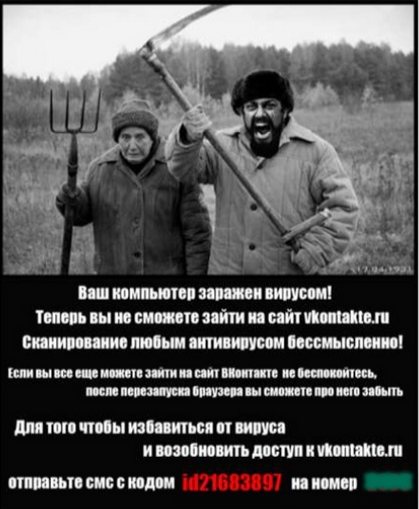
Or this (if you’re Russian):
… Or any of the thousands of other blocking screens similar to these, and for any platform – including Windows and Mac.
Several years ago the scale of the blocker epidemic got rather out of hand in Russia and ex-USSR countries, and in response blockheads started getting caught and sent to jail. Optimistically, turnover of this branch of computer crime in 2010 made up more than $3 million (pessimistically – more than $15 million), and the number of its victims reached the tens of millions! And out of that lot something like 5% of them actually paid the extortionists – who get a taste for the swag and high life, get more and more cocky, and get inspired to come up with new strains of blockhead malfeasance.
At the peak of the epidemic we released a free deblocker, available both as an app for mobile devices and as a web service. After entering the phone number or account of the extortionist given on the blocker, the deblocker generates an unblocking code, working a bit like ‘call a friend’. You’d think that the blocker epidemic might have been conquered once and for all with the advent of such a deblocker, but in fact no – the blockheads were just warming up…
It’s true that, judging by the number of visits to our deblocker web service, the scale of the scam on the whole has been reduced by around ten times. BUT… the problem in fact just got worse. Here’s how:
First: the initially uniquely Russian (post-Soviet) phenomenon went global (together with premium SMS numbers and e-money). As it did, Russian (post-Soviet) cyber-blockheads were able to hide from foreign justice due to the bureaucratic peculiarities of international cooperation.
Second: earlier, blockers were ‘honest’ (sic!), and after payment of the ransom they actually would remove banners from screens (until they decided to block next time). These days there’s no such code of honor, and the banners stay put after payment. And not just because the blockheads are mean like that today: in fact, there’s actually no code contained in blockers today for unblocking, so deblocker services are rendered redundant! Ouch!
So what’s to be done?
First of all, apart from rare exceptions, there still remains the possibility of ‘surgical intervention’ and manual removal of blockers with free utilities, should a full-fledged antivirus let an attack through. Now, if you read the abundant words at the other end of that link, you’ll understand that such surgery is far from an easy task, and one that needs sorting by specialists. So, as we’re wont to do, we decided to tear up the rulebook that says ‘specialist needed’.
Now users in KIS 2014 have a most wholesome feature which is able to remove a blocker with the help of just four fingers – your own four. Or three, but used several times :) No surgery. No specialist. And the icing on the cake: without those rare exceptions I mentioned.
How?
So:
For a couple of years already in KIS there’s been the Virtual Keyboard feature. This is an operating system driver that protects from keylogging. That is, even if a computer is infected with some super-duper Trojan or something, its attempts to intercept, for example, entered passwords, will be in vain, as keys aren’t physically pressed on the keyboard – they’re pressed on the Virtual Keyboard instead, which Trojans can’t see. Now we use this feature to fight blockheads and their blockers too…
Virtual Keyboard prevents blockers from taking full control over a keyboard. If the user enters the combination Ctrl+Alt+Shift+F4 (or Ctrl+Alt+Del several times) – Virtual Keyboard understands there’s an emergency situation and instructs KIS 2014 to launch the blocker deactivation procedure. Or, to be more precise, different antivirus components (signatures and heuristics) detect the infection and conduct a cleanup of the active processes and system registry, and unblock the screen. Then we delete the remains of the blocker with standard antivirus means, relaunch explorer.exe, and restore the ‘Start’ key (or whatever it is today) and the original desktop. Incidentally, the described scenario of blocker deactivation makes up the contents of our patent application currently undergoing expert examination.
Afterword
This summer a 21 year-old American became a blocker victim. This is what he found on his screen:
Eventually the guy turned himself into the police. It then transpired that there was in fact child porn on his PC. Well, as they say, you reap what you sow…