January 19, 2023
2022 review: patents coming on strong too!
Inventing cutting-edge new technology is only the half of it. Wait – no: let’s not be so categorical…
Cutting-edge new technology that’s oh-my groundbreaking sets in motion a life-cycle that’s probably a lot more complex and long-winded than might at first be imagined by many. Of course, without the invention in the first place there’d be nothing, but without the life-cycle that comes after it, even the most amazing revolutionary technology risks going belly up before it’s even gotten off the ground, never to help humankind in the way it could have. Alternatively, the invention could be at risk of falling into the hands of so-called consumer champions or patent trolls.
Among the many business functions that go into the mentioned life-cycle of new technology is that of patenting. For, alas, the system works whereby, if the new tech’s not patented, you don’t have any rights to it – even though you invented it! And history is full of such examples: the karaoke machine, magnetic stipes on plastic cards, fidget spinners, and a whole load more.
So – patenting. It happens to be by far not the simplest or most accessible of business processes, and it requires lots of expertise and lots of money – especially when you’re global. But that doesn’t make it any less necessary. And since our business at K has always been founded upon new technology, as soon as our bottom line allowed it – we straight away got into patent protection: in 2008 we got our very first patent. Ever since, little by little, we’ve been steadily growing our own patent expertise as much as we could allow ourselves down the years. And quite right too!…
The more successful the business became and the more we expanded around the world – all the more often patent trolls would come after us looking for the easy money. Also – unscrupulous competitors, despite having tech that could hardly compete with us on quality, still weren’t happy allowing customers use our products. Altogether, we were hit with 10 patent actions; nine we won; one is currently being considered. Because we never give in. We fight back – and win!
Overall picture.
The pandemic years and current geopolitical turmoil have of course negatively affected our business on the whole, and that has had a knock-on effect on our patent work – also down. And both past and current events look likely to echo into the future for years. However, that’s no reason to lie low until things get better; just the opposite – it warrants hitting the gas stepping on the proverbial accelerator all the harder! And that’s just what we did in 2022 (2021, btw, is here), despite everything. Let me tell you how…
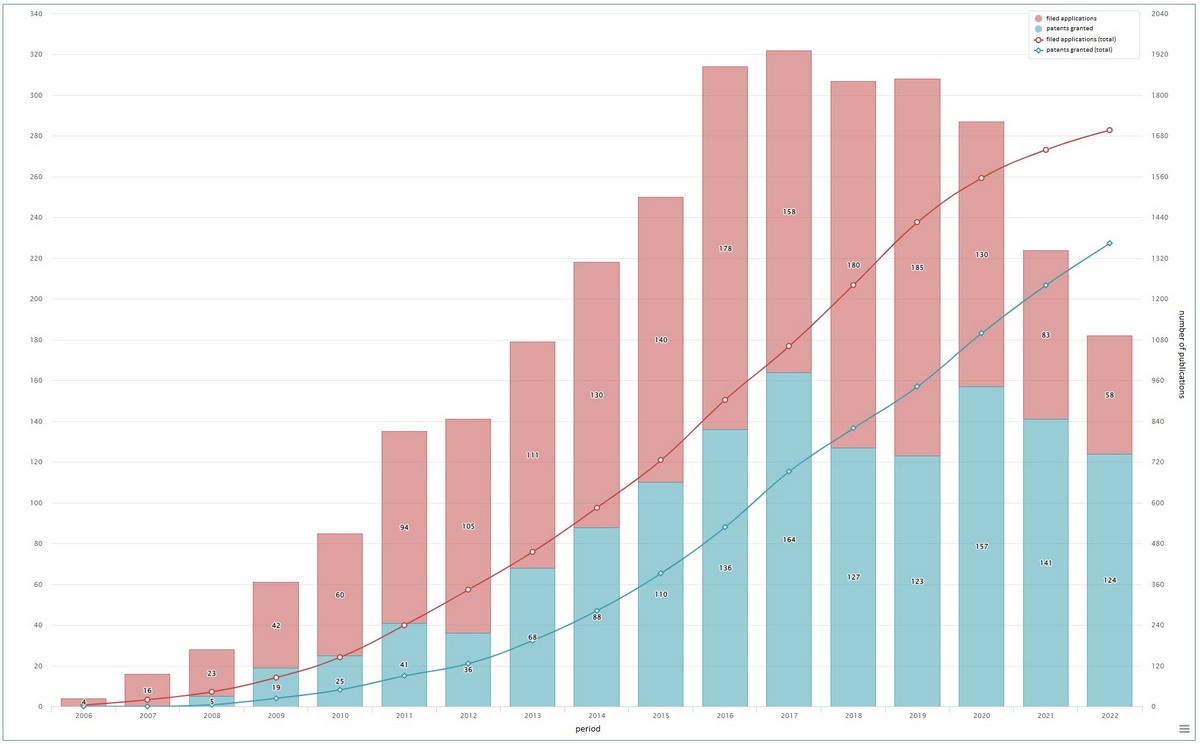
We finished last year with a portfolio of 1367 patents and 330 patent applications in different countries (including the U.S., the EU, Russia, and China). In 2022 we obtained 123 new patents (including in the U.S. – 51; Russia – 37; China – 24; the EU – 9), and submitted 58 patent applications. But let’s not concentrate just on quantity. Check out the quality too: we’ve been granted patents to ~98% of all our patent applications (in some countries – 100%!), while the world average for companies is somewhere around 50%. Go us!
Our overall patent picture looks like this:
Variation is the engine of progress.
So which technological segments were we submitting patent applications for the most? Actually, none really predominate. We simply seek patents for our tech when we come up with something new across the broad range of our cybersecurity technologies. Let me simply go through some of our more interesting patents (the tech that’s patented is in bold)…
Let’s take, for example, machine learning. This makes up 71 patents and 63 applications in all in our portfolio. Those include using machine learning to detect anomalies in production processes and thus reveal previously-unknown cyberattacks, as well as crashes, malfunctions and idle time of industrial equipment. This is all done by our “anomaly early-warning system” – MLAD (detail – here), which already has a full 10 patents to its name (and is sure to have plenty more in the future as it evolves).
As to (machine-learning patents in) 2022 in particular, we submitted a patent application for technology using diagnostic rules that describe earlier-known peculiarities of behavior of an object being monitored. Activation of rules is considered an anomaly, while an incident is classified by a special processor of events on the basis of neurosemantic networks for uncovering templates and anomalous sequences.
We filed plenty of patent applications for protecting our inventions connected to our anti-phone-spam application WhoCalls, which determines IDs of incoming-call numbers, their reputation, and category based on algorithms of machine learning and user verdicts. This mega-useful thing works on both Android and iOS to provide safe space for social interaction by phone.
For example, ion WhoCalls we use approaches for determining numbers based on the nature of calls from them, and use a Bloom filter in the collection of statistics on phone calls for depersonalization of data.
One of the fastest-developing IT segments in the world is that of the Internet of Things (IoT). The dynamic here is so crazy that new products are released so fast and furiously that, often, developers, to put it mildly, hardly even think for a moment about their cybersecurity. It’s like getting into fisty-cuffs first and only later deciding to talk things through to stop the fight and prevent the black eyes and broken noses. Meanwhile, who’s “stopping the fights”? That’s us! And there’s soooo much to patent here: it’s a field that’s largely unpatented!
Among the most interesting IoT patent applications: technology of intercepting traffic in IoT networks for determining anomalies and malicious objects, and a solution providing digital security for smart homes by installing protective solutions for smart devices.
What else, generally, is worthy of a mention? (i) There are the patents for sandbox optimization (used in Research Sandbox, KATA, etc.; in all in the portfolio: 106 patents and 24 applications) to reduce the load from dynamic analysis of apps; (ii) patents for using KasperskyOS to control industrial traffic; and (iii) patents for the technology of delivering messages inside KasperskyOS. Btw, in 2022 KasperskyOS was granted 20 new patents and five applications were submitted for it!
Need more? Then here are the very best of the best – the most interesting patents of the year:
US11514160: System and method for determining a coefficient of harmfulness of a file using a trained learning model.
This patent covers use of neural networks for forming rules for detection. For example, upon discovering an APT (targeted attack), usually there are just one or two uncovered malicious files to play with for analysis. After this discovery, similar malicious files need to be found – ones with some of the same attributes as the discovered files, but which may execute totally different actions. For this we use a special neural network that’s trained on a single malicious file and collections of safe files (to minimize false alarms and to further train the neural networks).
US11288401: System and method of reducing a number of false positives in classification of files.
A patent covering use of two classifiers in a row for finding malicious files. The analysis is split into two stages: in the first, easily extracted attributes are used (file sizes, section quantity, other info from the header of the file). On the basis of such attributes a hash is calculated – the number of the sector in the dimension of files. At the second stage, more accurate classifiers are used (for example, decision trees) on more complex data – analysis of strings, disassembly, use of statistical data. The second classifier for each sector is trained separately, thereby increasing its local precision.
US11449615: System and method of forming a log when executing a file with vulnerabilities in a virtual machine [aka – sandbox]. Also: US11379581: System and method for detection of malicious files.
The technology covered by these patents solves a different task connected with a sandbox: filtering analyzed files using machine learning, which permits reducing the load on infrastructure by way of filtering out polymorph files.
And in industrial cybersecurity (34 patents and 19 applications in all in our portfolio):
US11385987: System and method for assessing an impact of software on industrial automation and control systems – a special stand for the analysis of malware activity and its effect on ICS systems (details – here).
US11356468: System and method for using inventory rules to identify devices of a computer network – passive analysis of network traffic for identification of ICS objects together with context decoding of network packets.
Thank you for your attention folks! Patent overview-2022 – over and out…

