October 24, 2019
Threat Intelligence Portal: We need to go deeper.
I understand perfectly well that for 95% of you this post will be of no use at all. But for the remaining 5%, it has the potential to greatly simplify your working week (and many working weekends). In other words, we’ve some great news for cybersecurity pros – SOC teams, independent researchers, and inquisitive techies: the tools that our woodpeckers and GReAT guys use on a daily basis to keep churning out the best cyberthreat research in the world are now available to all of you, and free at that, with the lite version of our Threat Intelligence Portal. It’s sometimes called TIP for short, and after I’ve said a few words about it here, immediate bookmarking will be mandatory!
The Threat Intelligence Portal solves two main problems for today’s overstretched cybersecurity expert. First: ‘Which of these several hundred suspicious files should I choose first?’; second: ‘Ok, my antivirus says the file’s clean – what’s next?’
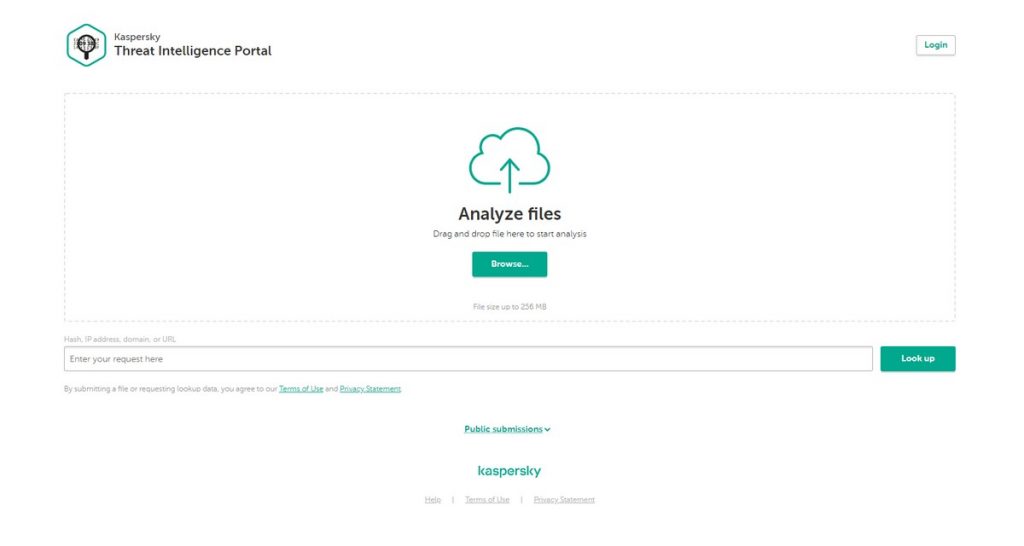
Unlike the ‘classics’ – Endpoint Security–class products, which return a concise Clean/Dangerous verdict, the analytic tools built into the Threat Intelligence Portal give detailed information about how suspicious a file is and in what specific aspects. And not only files. Hashes, IP addresses, and URLs can be thrown in too for good measure. All these items are quickly analyzed by our cloud and the results on each handed back on a silver platter: what’s bad about them (if anything), how rare an infection is, what known threats they even remotely resemble, what tools were used to create it, and so on. On top of that, executable files are run in our patented cloud sandbox, with the results made available in a couple of minutes.
At this point I can hear the 5% screaming: ‘It’s just VirusTotal!’
Yes – and no.
On the one hand, the aim is the same – to give specialists additional tools for analyzing a concrete incident and making an informed decision. On the other, our approach is completely different.
VirusTotal was conceived as a simple multiscanner – it aggregates various antivirus engines and feeds them with user-uploaded files. For that reason, the accusation ‘you don’t detect file X’ often gets hurled at all vendors, including us; but it’s more accurate to say that we don’t detect X with a traditional file scanner. As it later transpires, we successfully detect it using other tools. But on VirusTotal you simply won’t see that. Sure, additional tools have appeared on VirusTotal, but the general focus remains on broad coverage of engines employing a very conservative technology that was created 30-plus years ago.
As experts in deep analysis of complex threats, we strive to make this very depth available to the entire specialist community. The only engine that analyzes artifacts in the Threat Intelligence Portal belongs to the company that bears my name. And it happens to be the best in the world. It combines dozens of advanced analysis technologies (see here, here, here, and so on) and then lets you take a look at the detailed results. Of course, in comparison with the part of our engine that resides on VirusTotal, TIP gives a very different detection level.
In addition to that, it may be worthwhile to scan files with VirusTotal as well – a second, third, and fourth opinion is never a bad thing. But it’s vital to know how to properly weigh these opinions. Incidentally, if we ever decide to expand the Threat Intelligence Portal with information from a partnership with other vendors, our due diligence will be extra strict.
Another difference between the Threat Intelligence Portal and VirusTotal is… how to describe it… – the limited distribution of information. Files uploaded to VirusTotal are available to a wide range of subscribers, whereas with our Threat Intelligence Portal there are no subscribers with access to other people’s files.
On the topic of subscriptions:
There is a paid version of the Threat Intelligence Portal, which is much richer – in part because of the detailed reports on detected cyberthreats written up by our top analysts it gives access to. And if it turns out that an uploaded file resembles, say, a known piece of financial malware, the freshest and most detailed info about how its cyber-villain developers attack victims, what tools they use, and so forth, is available right there in the full version of the service.



