October 5, 2018
Cyber-paleontology: Sounds impressive; its results – more so.
Hi folks!
Let me kick off by paraphrasing a rather famous philosophical postulate: ‘Does a profession determine man’s social being, or does his social being determine his profession?’ Apparently this question (actually, the original) has been hotly debated for more than 150 years. And since the invention and spread of the Internet, this holy war only looks set to be extended for another 150, at least. Now, I personally don’t claim to support one side or the other; however, I do want to argue (based on personal experience) in favor of the dualism of a profession and being, since they mutually affect each other – in many ways and continually.
Toward the end of the 1980s, computer virology came about as a response to the growing proliferation of malicious programs. Fast-forward 30 years, and virology has evolved (rather, merged – in ecstasy – with adjacent fields) into the cybersecurity industry, which now often dictates the development of being IT: given inevitable competition, only the technology with the best protection survives.
In the 30 years since the end of the 1980s, we (AV companies) have been called quite a few different colorful and/or unsavory names. But the most accurate in recent years, IMHO, is the meme cyber-paleontologists.
Indeed, the industry has learned how to fight mass epidemics: either proactively (like we protected users from the largest epidemics of recent years – Wannacry and ExPetr), or reactively (using cloud-based threat-data analysis and prompt updates) – it doesn’t matter. But when it comes to targeted cyberattacks, there’s still a long way to go for the industry on the whole: only a few companies have sufficient technical maturity and resources to be able to cope with them, but if you add an unwavering commitment to expose any and all cyber-baddies no matter where they may come from or what their motives might be – you’re left with just one company: KL! (Which reminds me of something Napoleon Hill once said: ‘The ladder of success is never crowded at the top’.) Well it’s no wonder we’re in a lonely position (at the top of the ladder): maintaining that unwavering commitment to expose literally anyone is waaaaay more expensive than not maintaining it. And it’s waaaay more troublesome given the ongoing geopolitical upheavals of late, but our experience shows it’s the right thing to do – and users confirm this with their wallets.
A cyber-espionage operation is a very long, expensive, complex, hi-tech project. Of course, the authors of such operations get very upset and annoyed when they get caught, and many think that they try to get rid of ‘undesirable’ developers by using different methods via manipulation of the media. There are other, similar theories too:
But I digress…
Now, these cyber-espionage operations can remain under the radar for years. The authors take good care of their investments kit: they attack just a few specially selected targets (no mass attacks, which are more easily detected), they test it on all the popular cybersecurity products out there, they quickly change tactics if the need arises, and so on. It’s no stretch of the imagination to state that the many targeted attacks that have been detected are just the tip of the iceberg. And the only really effective means of uncovering such attacks is with cyber-paleontology; that is, long-term, meticulous collection of data for building the ‘big picture’; cooperation with experts from other companies; detection and analysis of anomalies; and subsequent development of protection technologies.
In the field of cyber-paleontology there are two main sub-fields: ad hoc investigations (after detecting something by chance and pursuing it), and systemic operational investigations (the process of planned analysis of the corporate IT landscape).
The obvious advantages of operational cyber-paleontology are highly valued by large organizations (be they state or commercial ones), which are always the primary target in targeted attacks. However, not all organizations have the opportunity or ability to undertake operational cyber-paleontology themselves: true specialists (for hire) in this niche line of work are few and far between – and they’re expensive too. We should know – we’ve plenty of them all around the world (with outstanding experience and world-renowned names). Thus, recently, given our strength in this field and the great need for it on the part of our corporate customers – true to the market principles of supply and demand – we decided to come up with a new service for the market – Kaspersky Managed Protection (KMP).
KMP, essentially, is our outsourcing of cyber-paleontology.
First, our cloud service collects metadata of network and system activity. This then gets aggregated with data from our KSN; then all that is analyzed by both smart systems and cyber-paleontologists experts (thus, the HuMachine approach).
Back to the collection of metadata… – what’s really cool about it is that KMP doesn’t require installation of extra sensors for the collection of metadata. The service works in unison with already installed products (in particular, KES and KATA; and in the future, potentially, other developers’ products), whose telemetry it uses as the basis of its ‘medical examination’ > diagnosis > treatment prescription.
But more interesting is what’s hidden in the aggregation with KSN data.
The service already has in its possession gigabytes of raw telemetry from different sensors: OS events, behavior of processes and their network interaction, activity of system services and applications, security products’ verdicts (including unusual behavior detection, IDS, sandboxing, objects’ reputation checking, Yara-rules… (head stopped spinning yet?!)). But if done properly, out of this chaos you can come up with techniques that can help eventually uncover targeted attacks.
At this stage, to separate the wheat from the chaff, we use patented technology of cloud detection, investigation and elimination of targeted attacks. First, received telemetry is automatically tagged by KSN as per the popularity of objects, a belonging to this or that group, similarities with known threats, and many other parameters. In other words, we filter out the chaff, and on all the useful stuff left (different grains of wheat) we attach special tags.
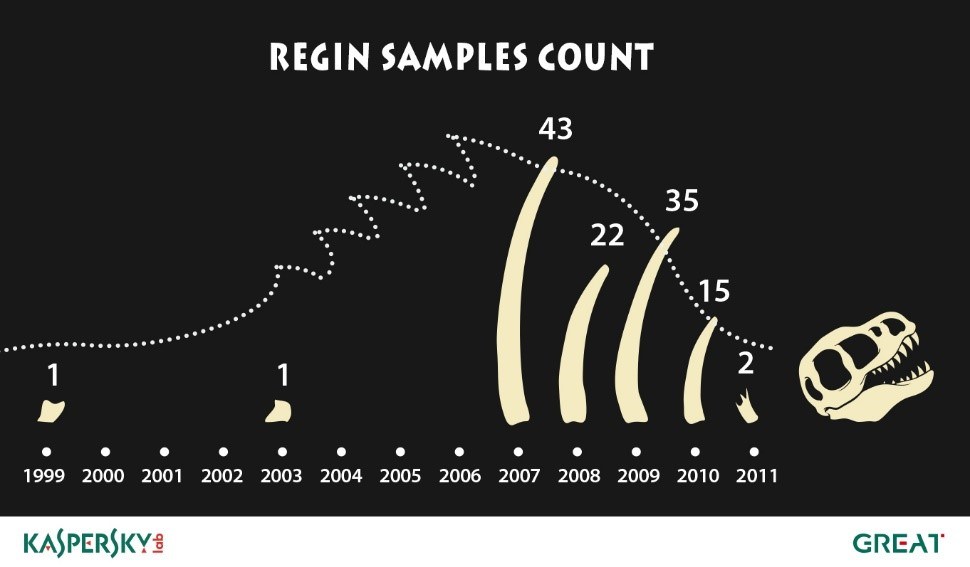
Then the tags are automatically processed by a correlational mechanism with machine learning, which puts forth hypotheses on potential cyberattacks. In the language of paleontologists, we study the dug up fragments to find similarities with already discovered dinosaurs, and also look for unusual combinations of fragments that could be characteristic of dinosaurs as yet unknown to science.
The correlational mechanism relies on a multitude of information sources for building hypotheses. Over the 21 years since we established KL we’ve accumulated… sufficient data (if I’m modest:) for such hypotheses, including: on suspicious statistical deviations from normal activity; on tactics, technologies and procedures of various targeted attacks; the data we glean from the investigations of computer crimes we participate in.
Once hypotheses are put together, the time comes to put the brains of the cyber-paleontologist to work. This expert does things artificial intelligence can only dream of: he/she checks the authenticity of the presented hypotheses, analyzes suspicious objects and actions, eliminates false positives, teaches machine learning robots, and develops rules for finding new threats. One day, though, practically everything that was once done manually by a paleontologist will be done automatically – it’s a never-ending process of conversion of experience in investigations, and of investigations becoming an automated service.
So, gradually, step-by-step, with the help of cutting-edge technologies and overseen by experts, out of tons of earth, traces can be found of hitherto unknown monsters targeted attacks. The more unprocessed earth KMP receives, and the further it digs back in time, the greater the likelihood of ‘discovering the undiscoverable’ and, accordingly, uncovering unknown attacks. What’s most important is that this is the most effective means of protection, since nowhere but in the networks of large organizations is there that unprocessed earth containing fragments of dinosaurs.
In closing, a few words on how KMP complements our Security Operations Center (SOC) – the control center for information security incidents.
Of course, KMP won’t replace SOC, but (i) it could give a push toward its creation, since it elegantly solves a single (though the most important) task: uncovering attacks of any complexity; (ii) it could expand the competence of an existing SOC by adding to it cyber-paleontology; and (iii) last but most: it could create extra business for MSSP providers by expanding the service applications of scalable functions of cyber-paleontology. I think this third factor may be the main vector in the development of KMP.