July 26, 2014
Cybernews from the dark side – July 26, 2014.
Remote controlled car – your car, while you’re driving it…
News about new hacks, targeted attacks and malware outbreaks is beginning to bore the general public. It’s becoming an incessant stream after all. What isn’t boring the life out of the general public is something a bit more unusual: stuff you wouldn’t dream could be hacked… getting hacked.
A report from China told how hackers broke into the Tesla motor car’s gadgetry – as part of a contest during a hacker conference. So, why Tesla? What’s so good about Tesla? Well, that’ll be its being an electric car, and its being crammed with so much ‘smart’ electronics that it hardly resembles an automobile than a mobile supercomputer. Still, what was Tesla expecting? Any new functionality – especially that developed without the involvement of IT security experts – will inevitably bring with it new threats via vulnerabilities, which is just what the hackers at the conference in China found.
The Chinese hack demonstrated the following: a malefactor could control the brakes and lights and more – even while the car’s moving. There’s your Watch Dogs in real life! No details regarding how this is possible have been published (and just as well). The details (allegedly) were responsibly sent directly to Tesla for fixing.
Hmmm, but let’s wait and see if it turns out that that really is what happened… After all, there have been numerous instances of things like this – where it turned out that the ‘hack’ was actually impossible, or only possible given some totally unrealistic conditions. Still, I won’t be surprised if the vulnerability turns out to be real: Just recently we carried out some real curious research into the ‘smart’ contents of a new BMW. In short, the potential for hacks there is aplenty.
Boomerang.
Now for some cybernews about passwords.
A WSJ journalist decided to put himself forward as a guinea pig to demonstrate the uselessness of passwords. (We use more progressive technologies of multi-factor authentication, including one-time passwords via text message!)
Now, I’ve nothing against 2FA: it rules (even though they’ve already learned how to get round it)! However, the experiment didn’t quite work out: the journalist published his Twitter password, after having activated automatic login confirmation to be sent to his cell. The account wasn’t hacked, but he quickly had to quit the experiment – those wanting to disprove his theory about the irrelevancy of passwords turned out to be so numerous that the journalist’s telephone ‘exploded’ with text requests!
Dangerous advice.
Passwords are a real hot topic. Here’s another gem from that part of the cyber-landscape.
How many web services do you use? And how many passwords have you got? The great majority have one of the latter – regardless of how many they have of the former. Yes, we use the same password for just about everything; what’s worse – not only for the Internet, but also for access to corporate networks. But that’s only natural: remembering dozens of passwords is simply impossible to most of us.
So what’s to be done?
Well, Microsoft has come up with a reliable mathematical model to manage all accounts with the use of just a few passwords. What you do is split up all the web services you use into groups in terms of their importance and then give each group its own password – the more important taking the strongest passwords. There’s one important proviso: the model isn’t recommended for online banking or other services that give off just a whiff of Benjamins (hardly an insignificant provisio, but I’ll not dwell…:).
Still, if you’re not sure about the idea (“if it can’t protect my online banking what use is it for my emails??!!”), there’s a much simpler (and more reliable) solution – a password manager.
I know what your OPC is doing this summer.
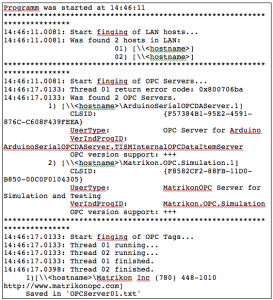
Back to the security of industrial control systems (ICS).
I make predictions in this neck of the cyber-woods, and, alas, sometimes they come true. Among many I jinxed the appearance of malware for ICS, so now I view Cassandrism with caution. Still, every item of news from this spot of the cyber-forest either causes massive facepalm or goose bumps – or both.
Malware is getting dangerously close to ICS. And here’s one more bit of proof: a recently discovered module of the Havex Trojan scans OPC servers (‘interpreters’ between programmable logic controllers and the control system). That is, Havex can get into a corporate network (for example, via the bookkeeper’s computer), and then the cyberswine can get to know all about your industrial processes.
The good news: it looks like this module of Havex is nothing but some concept malware: its use in combat mode hasn’t been detected. All the same, there’s no doubt about the operability of this function. And in the security industry it’s a very short distance between theory and practice.
Another moneylending villain one bites the dust.
One more botnet: killed. Together with Europol, the FBI, GCHQ and others, we shut down Shylock. Shylock is no more. The complex operation took loads of planning and involved collecting and analyzing tons of information. It also ran simultaneously in many countries. But the best thing about it is it worked – meaning international cooperation, which I’ve been banging on for years about, also works!
Just five years ago such joint ops were done hardly ever, and accompanied with loud bureaucratic howls of displeasure. Ten years ago they were totally unrealistic because of the then very closed nature of cyber-police and lack of resources – including staff.
Java – worth the bovver?
Same old, same old, I know. Java’s everywhere; it’s practically impossible to avoid it; many services simply stop working without it. So the abundance of Java vulnerabilities, bugs and, as a consequence platform-specific malware and attacks makes things all the more unpleasant for all. Here’s the paradox: it was – believe it or not – planned to be the world’s most secure platform! Today of course it is well known for one thing: being insecure! It seems Oracle hasn’t been able to grapple this security issue to the ground. One gets the impression that after acquiring Sun, Java security was put onto the back burner.
I wonder: who’s disabled Java in their browsers?
Poll by @e_kaspersky: Who disabled Java in their browsers?Tweet
To those who haven’t turned it off – quickly patch it!