September 29, 2014
The evolution of OS X malware.
Is there any (Mac) OS X-specific malware around?
Oh yes. But for some odd reason I haven’t said anything interesting on this topic for quite a while…
The last time was two and a half years ago. Yes, that’s how long it’s been since the global Flashback worm outbreak that infected 700 thousand Macs worldwide. The security industry made quite a bit of noise about it (and quickly disabled the Flashback botnet), but since then – mostly silence… It might seem to some that ever since there’s been a complete lull on the Mac-malware front and not one bit of iMalware has disturbed Apple Bay’s calm waters…
But they’d be wrong…
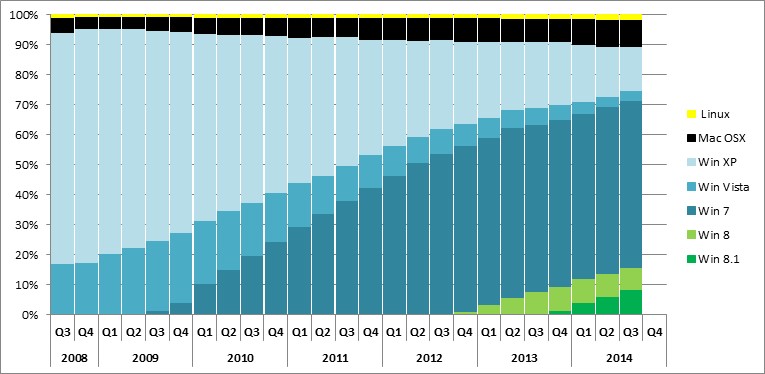
Sure, if you compare the threat levels of picking up some malware on different platforms, at the top of the table, by a long way, as ever, is the most widely used platform – Microsoft Windows. Quite a way behind it is Android – a relatively new kid on the block. Yep, over the past three years the cyber-vermin has been seriously bombarding the poor little green robot with exponentially increasing levels of malicious activity. Meanwhile, in the world of iPhones and iPads, except for very rare cyber-espionage attacks, there have been hardly any successful attacks thereon (despite using various exotic methods). It’s a similar story with Macs too – things are relatively peaceful compared to other platforms; but of late there have been… stirrings – about which I’ll be talking in this post.
Briefly, a few numbers – kinda like an executive summary:
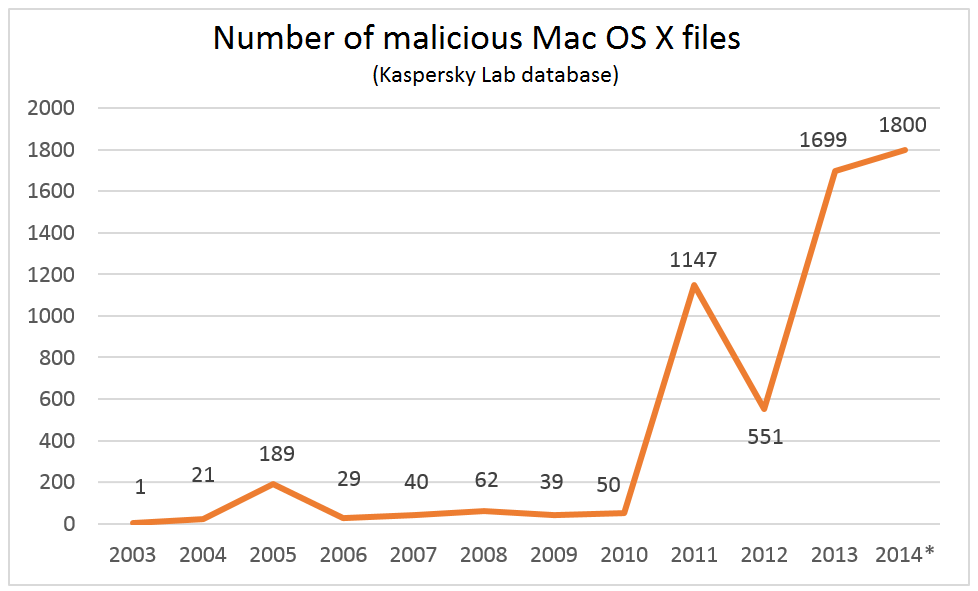
- The numbers of new for-Mac malware instances detected in the last few years are already in the thousands;
- In the first eight months of 2014, 25 different ‘families’ of Mac malware were detected;
- The likelihood of an unprotected Mac becoming infected by some Mac-specific-unpleasantness has increased to about three percent.
In 2013 alone @kaspersky detected ~1700 malware samples for OS XTweet
Now, if you dig deeper and look at the situation from the inside, from the point of view of a malware expert, the picture is much less rosy…
Mac-threats have evolved, the perception of security among Mac users has changed (but not too much), and the main question is what can we expect in the future? So here we go, without emotion, with just numbers and facts, for some unprejudiced analysis. And if you’re on for impartial, passionless discussion in the comments – please, be my guests!
First up – frontline reports.
So what’s been going on in the Mac-threat world in recent years? I’ll start off with the following graph. It shows the number of malicious files for OS X we’ve discovered over the years.
As you can see from the graph, just four years ago the year’s ‘catch’ of maliciousness was just 50, but then in 2011 there was a sudden surge, and ever since the annual cull has been counted in the hundreds – almost thousands.
So what exactly gets caught?
Well, in the first eight months of this year we detected nearly a thousand unique attacks on Macs, grouped into 25 major families. A few words on the most interesting:
- Backdoor.OSX.Callme – spreads in the body of a specially crafted MS Word document, which when launched installs a backdoor in the system via a vulnerability. This gives the attacker remote access to the system. At the same time it steals contact lists, apparently to search for new victims.
- Backdoor.OSX.Laoshu – it takes screenshots once a minute. It was signed with a trusted certificate of the developer. It looks like the virus writers were planning on uploading it to the App Store.
- Backdoor.OSX.Ventir – a multi-modular Trojan-spy with hidden remote control. It contains a keylogger based on open sourced logkext driver.
- Trojan.OSX.IOSinfector – installer of the mobile version of Trojan-Spy.IPhoneOS.Mekir (OSX/Crisis) – yup, it infects iPhones.
- Trojan-Ransom.OSX.FileCoder– the first file encryptor for OS X. Only just working – a buggy prototype.
- Trojan-Spy.OSX.CoinStealer– the first bitcoin-stealing malware for OS X. Disguises itself as a few open source bitcoin utilities. What it really does is install a malicious browser extension and/or a patched version of bitcoin-qt (an open source utility for mining bitcoins).
#malware for OS X you’ve never heard about (but might find on your Mac)Tweet
At this point a logical deduction may be: ok, ok, there’s some malware for Macs these days, but is it really a significant threat to users? How likely is an infection on an unprotected Mac? And which is the most prevalent malicious program?
Thanks to KSN, we’ve got the answer. But before analyzing the numbers, first, an important disclaimer: these data come exclusively from users of our products. Trying to work out how malware is spread globally, including among users of other security products and/or those with no antivirus – that’s both a thankless and very approximate task based on extrapolations from data from different sources. Nevertheless, it’s still worth digging into KSN data, if only to give us something to talk about by the water cooler :).
So, the top-20 detections of for-OS X malware for 2013–2014 (worldwide):
| Name | Number of detections | % |
| AdWare.OSX.Geonei.b | 56,271 | 39.15 |
| Trojan.OSX.Vsrch.a | 28,222 | 19.63 |
| AdWare.OSX.Geonei.d | 23,904 | 16.63 |
| Trojan.OSX.Yontoo.i | 7595 | 5.28 |
| AdWare.OSX.FkCodec.b | 6395 | 4.45 |
| Trojan.OSX.Yontoo.h | 3636 | 2.53 |
| Trojan.OSX.Yontoo.j | 3366 | 2.34 |
| AdWare.OSX.Geonei.c | 2889 | 2.01 |
| Trojan.OSX.Yontoo.a | 2079 | 1.45 |
| AdWare.OSX.Geonei.e | 1758 | 1.22 |
| Trojan.OSX.FakeCo.a | 1413 | 0.98 |
| Trojan.OSX.Okaz.a | 1126 | 0.78 |
| Trojan-Downloader.OSX.Vidsler.a | 868 | 0.60 |
| RemoteAdmin.OSX.AppleRDAdmin.c | 677 | 0.47 |
| AdWare.OSX.Bnodlero.a | 656 | 0.46 |
| Trojan.OSX.Yontoo.b | 633 | 0.44 |
| AdWare.OSX.FkCodec.a | 609 | 0.42 |
| Trojan-Downloader.OSX.FavDonw.c | 571 | 0.40 |
| AdWare.OSX.Geonei.a | 544 | 0.38 |
| Trojan.OSX.Yontoo.d | 533 | 0.37 |
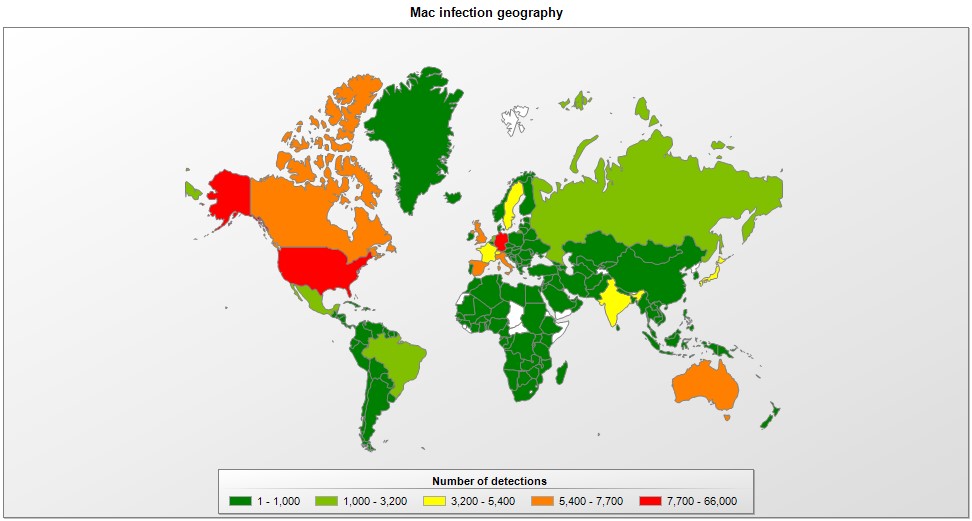
And here – the geography of iMalware for the same period:
Now, if you look at the above data closely, you’ll see that about half of the detections are made up of adware, while two-thirds of all of them are made up of only the first three malicious programs. As to the geography of the distribution of iMalware, on the whole it matches the popularity of Macs themselves, i.e., with prevalence mostly in developed countries – where potential victims have the most money overall. Lastly, curiously, the famous Flashback is missing from the top-20.
So what can we deduce from these data?
First: cybercriminals find it easiest making money with mostly legal (well, almost legal) approaches. Persistent advertising also makes money, and coupled with large-scale infections – big money.
Second: OS X virus writers are a fairly rare but sophisticated species. Unlike the Windows virus scene, the OS X virus scene bypassed the childish stage of ‘viruses for fun’ and went straight to the grown-up – Mac OS – stuff with all the attendant hardcore malware tricks that are necessary for it. These are serious folks, folks! It’s very likely they honed their skills on the Windows platform first, and then went over to Mac to conquer new, uncharted territory in search of new untapped money-making possibilities. After all, the money’s there, and the users are relatively blasé about security, which means there are plenty of opportunities – for those blackhatters who are willing to put in the work.
Third: professional espionage groups have really taken to exploiting OS X. Many APT attacks in the last few years acquired Mac-modules, for example Careto, Icefog, and the targeted attacks against Uyghur activists. Yes, here we’re talking pinpointed – exclusive as opposed to mass – attacks, aimed at specially chosen victims; this is why they don’t figure in the top-20. Not that they are any less dangerous; especially if your data may be interesting to intelligence agencies.
Now let’s figure out the practical relevance of the above stats.
Indeed, against the backdrop of the massive scale of disasters in the world of Windows, a hundred thousand detections in 18 months doesn’t look so bad, and might easily lead one to conclude that there really isn’t much of a threat at all. Well, there’s almost no threat. But does ‘almost no’ mean iUsers can relax and rely security-wise on Apple itself alone? In other words – not bother with protection at all? Read on…
To understand here who’s paranoid and who’s not paranoid wrong :), we again need to turn to KSN data. This time to consider the level of infestation – or the ratio of the number of protected Macs to the number of unique detections of Mac malware.
Within the month of August, the chances of picking up an iNuisance were around 3%. Not so bad compared with the 21% chance of infection for Windows users (based on KSN data). Still, this translates to one iMalicious program taking a peek at an active Internet user’s Mac 10 times a year.
Now things get even more interesting…
First: iUsers are not only being targeted by iMalware. Some types of attacks don’t care what OS a comp has. For example, phishing and MITM attacks. And these happen to be very widespread threats. They’re most interested in users’ bank accounts, key web services used, and activity on social networks.
Second: Macs are coming under attack from un-Mac-ish threats of another kind – those coming through holes in third-party software; for example, Java, Flash or Silverlight. This isn’t default software on a Mac, but still many users download and install it, so as to take full advantage of all the charms of the Web.
It’s hard to say what the percentage likelihood of an attack would become if we take into account all common third-party software. But I think it’s safe to say it would increase several-fold.
Mac-specific malware is not the only threat for Macs. There’s also phishing, MitM & 3rd party s/w vulnsTweet
Third: well, this isn’t quite about malware threats. Antivirus software long ago stopped being a thing in the background that somehow unnoticeably saves us from this or that. Modern antivirus contains many other useful features that go far beyond the canonical concept of the software. For example, parental controls, password managers, Wi-Fi reliability checks, webcam blocking, and hundreds of other features. It’s true that for-Mac security products lag behind their PC-cousins in terms of functionality, but slowly and surely they’re catching up…
And now for a bit of futurology…
Two questions have been asked constantly by many for a long time: Why is there so little malware for Macs, and will things get worse?
I have said many times that there are three essential conditions for the existence of malicious software on a particular platform: (i) the platform needs to have insecure architecture and thus vulnerabilities; (ii) it needs to be fairly widespread; and (iii) it needs to provide tools for third-party application development. OS X falters on item (ii) only.
‘Ha!’ says the knowledgeable reader. But there are now more than 80 million computers running Mac OS! Surely this is widespread enough? It might seem it. But then there are 1.5 billion Windows comps out there!
I’ve written about the economics of the computer underground before on these blog-pages. There’s a basic rule that applies to all operating systems, and that includes OS X: For the cyber-scum there’s no sense in spending resources on trickier, less popular OS’s when before them are tens of millions of fertile Windows-based computers – some without antivirus, most never updated, and others with free – and holey – antivirus. Put another way – the pickings are too easy with Windows. Why try harder (with OS X)?
What we should be looking at instead is where the critical mass might lie – where ‘minor’ (judging by their market share) OS’s like OS X become economically interesting. I’ve mentioned in the past that 5-7% of the global installed base should be the critical mass level. But that’s turned out to be too low. This year OS X has come up to close to 10%. Yet still there’s been no major change in the do-nothing little stance of the virus writers – only a few stirrings: clumsy, reluctant, and proof-of-concept stirrings.
Extrapolating the trend, in three years Apple could take up 15 percent of the market. Will that be the trigger for a rapid flurry of development of iMalware?
I don’t know. For a sharp increase – probably not. But an increase – for sure. Anyone have their own predictions on this?
So what will happen when the market share of OS X finally reaches its critical mass?
I think that first off there’ll be a few major epidemics with significant numbers of victims and significant monetary losses. Then there’ll be a chain reaction – virus writers will copy others, seeing how doable and profitable attacking OS X has become – and will switch en masse over to the platform.
Another possible scenario could be things suddenly getting out of control through an APT attack against OS X; for example, a global outbreak caused by a bug undocumented feature of malware or a leak of the technology of an attack, its spread on the computer underground, and the appearance of loads of clones.
The real situation with Mac security is difficult to estimate because most Mac users are still fully confident in the saintliness and infallibility of their favorite vendor. So what’s really going on on tens of millions of unprotected Macs is unknown. It’s pretty much like the underwater part of an iceberg. And sometimes this part brings unexpected and unpleasant (Titanic!) surprises like the Flashback worm in March 2012. But what malware is still there? What’s it doing? And who’s pulling the puppet strings – the usual cyber-crims, or white collar folks using hired programmers? All interesting questions, and we’re gradually going to find out the answers. But we need your help. We can’t save you forcibly. So take care of your own security by yourselves – at least take the first step and change your attitude to Mac protection!
In the meantime, here are a few simple tips for how to maintain your Mac’s hygiene and keep it secure.
A few simple tips for how to maintain your Mac’s hygiene and keep it secureTweet
That’s about it about Mac security discussion for now – but stay tuned. There’ll be more, soon, for sure, on this front – and ever more interesting…
P.S. Wow, that was quick! The ‘more on this interesting front’ turned up sooner than I expected!…
Researchers have found a massively serious vulnerability in Bash shell code, affecting Linux, UNIX, and – you guessed it – OS X. Patches are being hastily worked on, but so far there’s not been much progress. Let’s not forget that Unix is run on many industrial control systems and energy grids worldwide. Anyone remember Blaster? Back then Microsoft released a patch a month before the catastrophe… and by catastrophe I’m not hyberboling – it was a grandiose blackout of eastern USA.