April 1, 2013
New viruses from Chelyabinsk so advanced they blow the mind.
Every day our valiant antivirus lab processes hundreds of thousands of files. Each single day! Admittedly, some of them turn out to be clean and honest files, or just broken code, innocent scripts, assorted scraps of data, etc., etc., etc., but mostly it’s maliciousness – a lot of which is analyzed and processed automatically (as I’ve already mentioned on these cyberpages).
But every now and again we come across some reeeaaal unusual items – something totally new and unexpected. Something that activates the little grey cells, makes the heart beat faster, and gets the adrenaline pumping. I mean things like Stuxnet, Flame, Gauss and Red October.
Anyway, it looks like we’ve found something else in this original-oddity category…
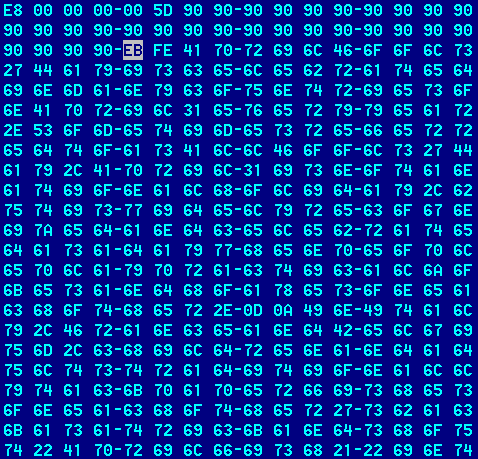
Yes, we’ve detected another malware-monster – a worm originating from the cyberstreets of the Russian Internet. What we were able to say straight off was that it surpasses in sophistication by a long way not only all known malicious programs today – including professional cyberspies and cyberweapons – but also any other known software – judging by the logic of the algorithms and the finesse of their coding.
Yes folks, this is big!
We’ve never come across such a level of complexity and perplexity of machine code with program logic like this. Analyzing the most complicated worms and Trojans normally takes several weeks – whereas this baby looked like it’d take years! Maybe several years!!! It’s just so darn elaborate and convoluted.
I don’t know a single software company that would have been able to develop such a beast. Nor any cybercriminals with their mostly primitive malware. Nor any of the secret services assumed to be behind the more artful malware that’s appeared in recent years. No. This new find simply cannot be the work of any of those three.
So… Are you sitting down? No? Change that.
I’d say it’s theoretically impossible to say that this code was written by a human being (glad to be seated now?).
This code is so infernally intricate that I fear this newly-discovered worm must have extraterrestrial origins.